
ICS and SCADA: The Backbone of Critical Infrastructure and How Infrastructure VAPT Secures Them
Industrial Control Systems (ICS) and Supervisory Control and Data Acquisition (SCADA) networks form the technological foundation of modern industrial operations. They manage and monitor critical infrastructure across diverse sectors, including energy, manufacturing, transportation, and water treatment.
Despite their operational significance, the growing integration of ICS and SCADA with IT networks and the rise of advanced cyber threats have made their security a top priority.
Security Challenges in ICS and SCADA

ICS and SCADA systems face unique challenges that distinguish their security needs from traditional IT networks:
1. Legacy Systems
Many ICS/SCADA components are decades old, designed before cybersecurity was a primary concern. Retrofitting them with modern security features can be difficult and costly.
2. Operational Continuity
Downtime in ICS environments is often unacceptable, as it may disrupt critical services or endanger public safety.
3. Proprietary Protocols and Systems
Custom protocols like Modbus, DNP3, and OPC are common in ICS/SCADA environments, requiring specialized knowledge for security assessment.
4. Interconnected Environments
The convergence of IT and operational technology (OT) increases the attack surface, exposing ICS/SCADA systems to external threats.
5. Targeted Attacks
Nation-state actors and sophisticated hackers often target ICS/SCADA systems due to their strategic importance, as seen in incidents like Stuxnet, BlackEnergy, and Triton.
Focus Areas for ICS/SCADA Penetration Testing
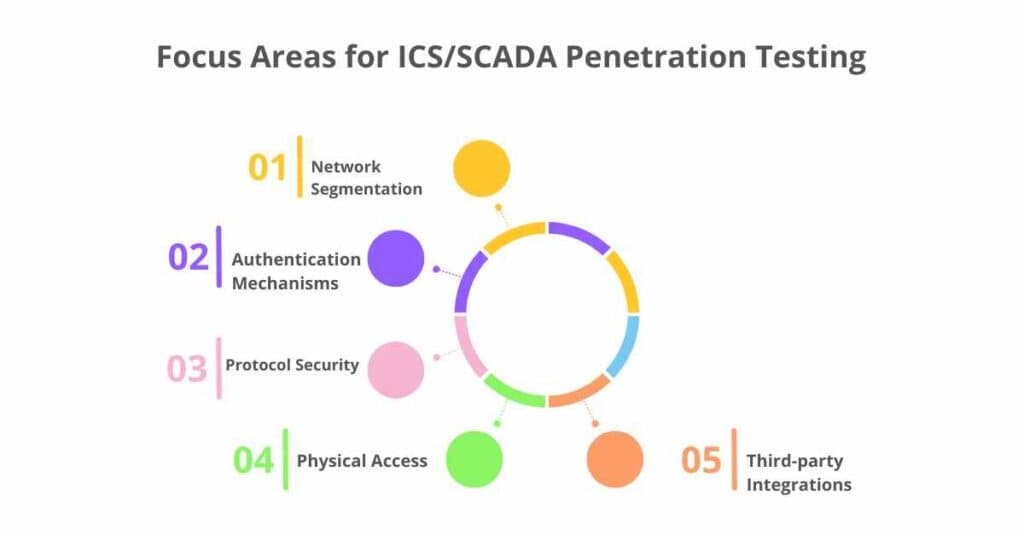
1. Network Segmentation
Ensuring proper isolation between OT and IT networks to limit lateral movement of threats.
2. Authentication Mechanisms
Testing the robustness of user access controls and credential management systems.
3. Protocol Security
Evaluating the security of SCADA-specific protocols like Modbus and OPC UA against attacks such as spoofing or data tampering.
4. Physical Access
Assessing physical security measures to prevent unauthorized personnel from accessing critical components.
5. Third-party Integrations
Examining vendor systems, remote access solutions, and supply chain dependencies for potential vulnerabilities.
Key Benefits of Infrastructure VAPT in ICS/SCADA Security
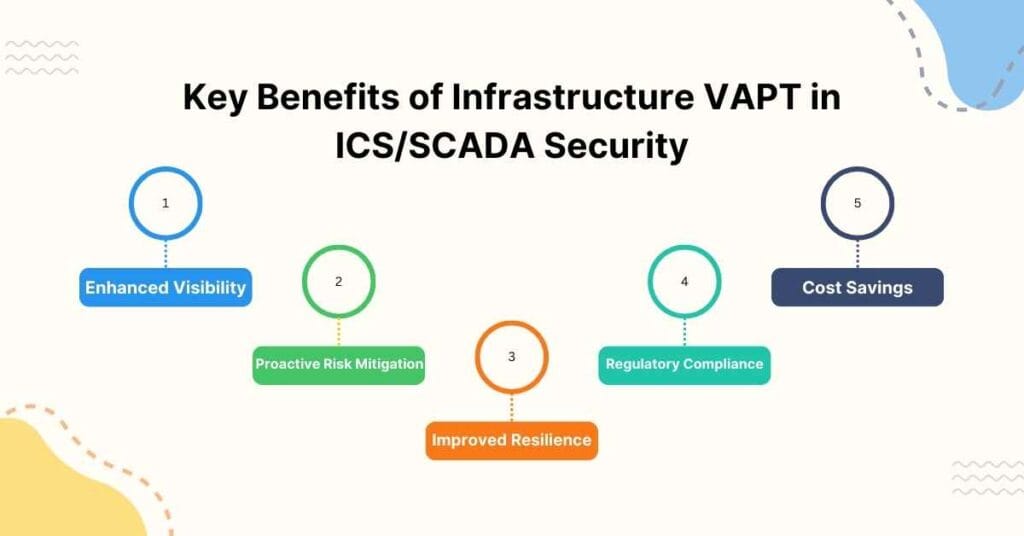
1. Enhanced Visibility
Identifies vulnerabilities across networks, devices, and protocols, offering a clear understanding of the attack surface.
2. Proactive Risk Mitigation
Addresses vulnerabilities before they can be exploited by adversaries, reducing the likelihood of operational disruption or physical damage.
3. Improved Resilience
Strengthens the system’s ability to withstand targeted cyberattacks, ransomware, and insider threats.
4. Regulatory Compliance
Demonstrates adherence to industry standards and regulatory requirements, avoiding fines and reputational damage.
5. Cost Savings
Reduces the long-term cost of security by preventing incidents that can result in operational downtime or equipment damage.
Steps to Conduct Infrastructure VAPT for ICS/SCADA
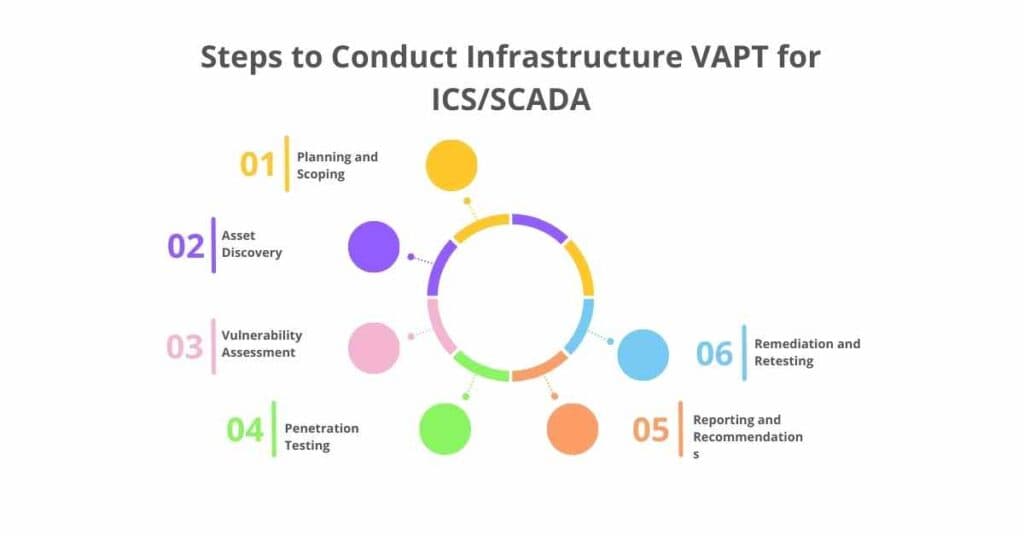
1. Planning and Scoping
- Define the scope of the assessment, focusing on critical components and high-risk areas.
- Establish rules of engagement to ensure minimal impact on operational systems.
2. Asset Discovery
Create an inventory of all devices, networks, and protocols used in the ICS/SCADA environment.
3. Vulnerability Assessment
Use specialized tools and techniques to identify vulnerabilities without affecting system performance.
4. Penetration Testing
Conduct controlled exploitation of vulnerabilities in a safe and secure manner.
5. Reporting and Recommendations
Provide a detailed report outlining vulnerabilities, exploitation results, and prioritized remediation steps.
6. Remediation and Retesting
Address identified vulnerabilities and retest to confirm the effectiveness of implemented fixes.
Conclusion
Industrial Control Systems and SCADA networks are the lifeblood of critical infrastructure, making their security paramount. Infrastructure VAPT offers a structured and effective approach to identifying vulnerabilities, mitigating risks, and strengthening defenses in these complex environments.
By integrating VAPT into their cybersecurity strategies, organizations can protect their operations, ensure public safety, and maintain the trust of stakeholders in an increasingly interconnected world.
