
Broken Authentication: Common Errors and Fixes in APIs
APIs are the backbone of modern applications, enabling seamless communication between services. However, weak authentication mechanisms can turn them into prime targets for attackers. Broken authentication is one of the most common API security vulnerabilities, often leading to unauthorized access, data breaches, and account takeovers.
In this blog, we explore Broken Authentication: Common Errors and Fixes in APIs and common authentication mistakes businesses make in their APIs and how CyberSapiens helps strengthen security through expert API Vulnerability Assessment and Penetration Testing (VAPT) services.
Understanding Broken Authentication in APIs
Broken authentication occurs when authentication mechanisms are improperly implemented, allowing attackers to bypass security controls. This vulnerability can lead to:
- Unauthorized access
- Account takeovers
- Data breaches
- Privilege escalation
Common causes include weak password policies, poor session management, insecure API key storage, and flawed token validation.
Attackers exploit these weaknesses using brute-force attacks, credential stuffing, session hijacking, and token replay attacks. To safeguard API security, implementing strong authentication measures is crucial.
Common API Authentication Mistakes and Their Fixes
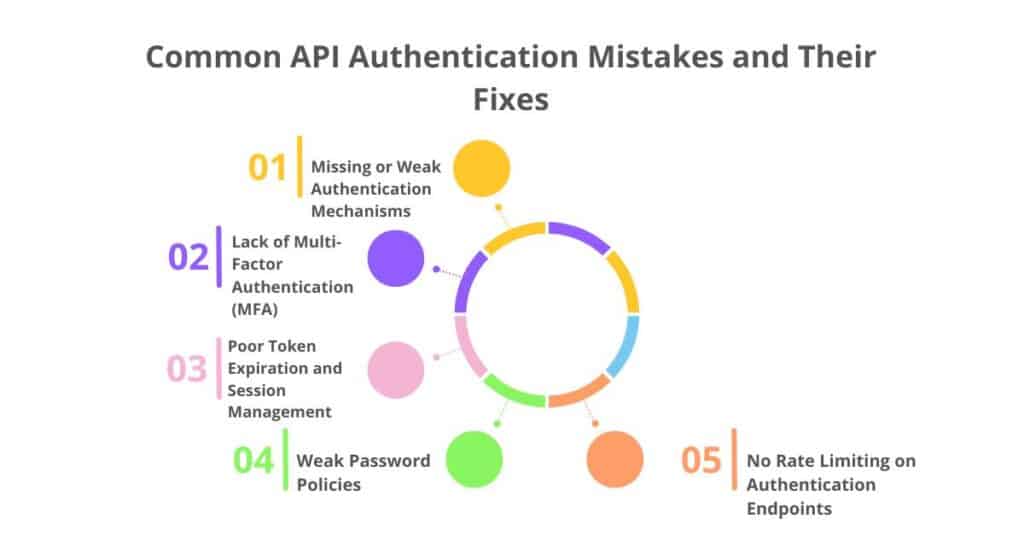
1. Missing or Weak Authentication Mechanisms
APIs without authentication expose sensitive data to unauthorized users. Attackers can directly access endpoints without credentials, leading to data leaks. Weak authentication methods make it easier for unauthorized users to exploit APIs.
📌 Example:
A public API allows anyone to fetch user profiles without authentication. Attackers can enumerate user IDs and access private information. Without authentication enforcement, personal data becomes easily accessible.
2. Lack of Multi-Factor Authentication (MFA)
Relying solely on passwords makes APIs vulnerable to credential-based attacks. Without MFA, a leaked password grants full access to user accounts. Implementing MFA significantly reduces the risk of unauthorized logins.
📌 Example:
An API allows login with only a username and password. If credentials are leaked in a data breach, attackers can access user accounts. Adding MFA would require an extra authentication step, enhancing security.
3. Poor Token Expiration and Session Management
APIs using long-lived tokens without expiry increase the risk of misuse. If an attacker steals a valid token, they can maintain access indefinitely. Proper session management prevents unauthorized prolonged access.
📌 Example:
A JWT token remains valid for a year, allowing attackers to reuse it if stolen. Even if the user logs out, the token remains active. Implementing short-lived tokens with refresh mechanisms enhances security.
4. Weak Password Policies
Allowing short or predictable passwords makes brute-force attacks easier. Without complexity requirements, attackers can guess passwords quickly. Enforcing strong passwords reduces unauthorized access risks.
📌 Example:
An API allows users to set “password123” as their password. Attackers can use automated scripts to guess weak passwords. Enforcing length and complexity rules strengthens authentication security.
5. No Rate Limiting on Authentication Endpoints
APIs without login attempt restrictions allow brute-force attacks. Attackers can try multiple username-password combinations without being blocked. Rate limiting helps prevent automated login abuse.
📌 Example:
An API allows unlimited login attempts without delays. Attackers use credential stuffing to test thousands of passwords. Adding rate limiting and CAPTCHA prevents such automated attacks.
How CyberSapiens Enhances API Security?
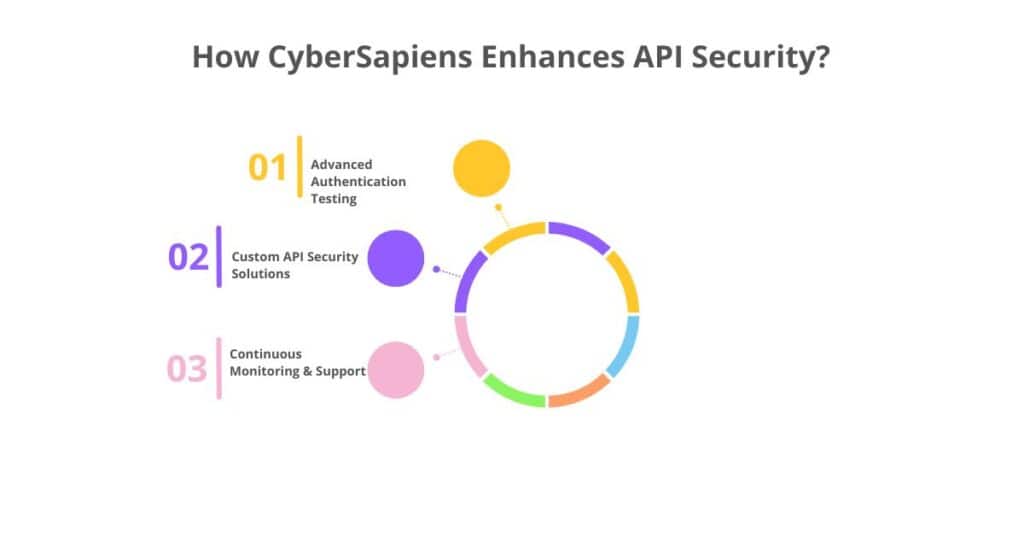
1. Advanced Authentication Testing:
Identifying broken authentication issues through rigorous security testing.
2. Custom API Security Solutions:
Developing tailored security strategies based on business needs.
3. Continuous Monitoring & Support:
Providing ongoing assessments and proactive security measures to ensure long-term API protection.
Protect Your APIs Before Attackers Exploit Them
Broken authentication can result in serious security breaches and financial losses. Don’t wait until it’s too late. Secure your APIs today with CyberSapiens’ API VAPT services.
- Email: sales@cybersapiens.co
- Phone: +91 6364011010
- Website: www.cybersapiens.co
Ensure your APIs are safeguarded with CyberSapiens. Your trusted partner in API security!
