
Rate Limiting: Why its Crucial for API Security and How to Implement It?
As penetration testers, we tend to discover APIs revealing more than endpoints they reveal the backend to be abused if there are not proper safeguards such as rate limiting. Developers may view rate limiting as a performance feature, but in security testing, it is a primary defence against abuse, brute-force, and denial-of-service (DoS) attacks.
This blog breaks down what Rate Limiting: Why its Crucial for API Security and How to Implement It for weak or missing rate limits during VAPT.
What is Rate Limiting in API Security?
Rate limiting is the practice of limiting the number of requests a client (IP, user, token, etc.) makes to an API within a time window. It prevents abuse by attackers attempting to:
- Brute-force authentication or password reset endpoints
- Scrape sensitive information
- Initiate resource-intensive actions
- Overload the system (DoS)
In pentesting, improper rate limiting is a critical discovery because it allows attackers to automate and scale quickly
Why It Matters for Security?
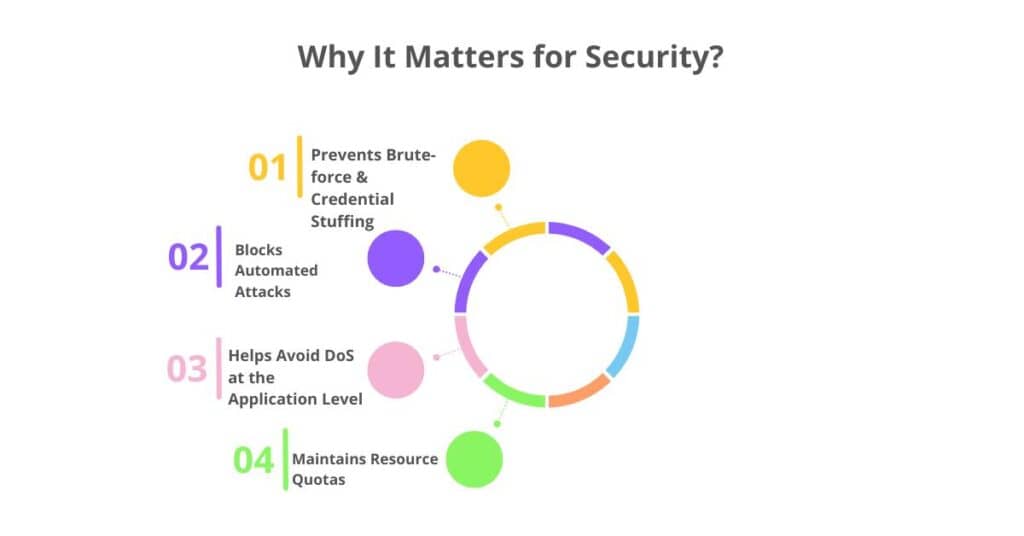
1. Prevents Brute-force & Credential Stuffing
Endpoints like /login, /verify-otp, /forgot-password, and /2fa are prime targets. Without rate limits, an attacker can script login attempts using leaked credential dumps.
2. Blocks Automated Attacks
Bots or malicious scripts can abuse APIs to scrape data, spam endpoints, or test for business logic flaws without being slowed down.
3. Helps Avoid DoS at the Application Level
Even without full-on DoS attacks, excessive API requests can degrade performance or crash systems.
4. Maintains Resource Quotas
APIs with compute-heavy or third-party integrations (e.g., payment, SMS, OTP) need rate limits to avoid high costs or system abuse.
How Penetration Testers Identify Weak or Missing Rate Limiting?
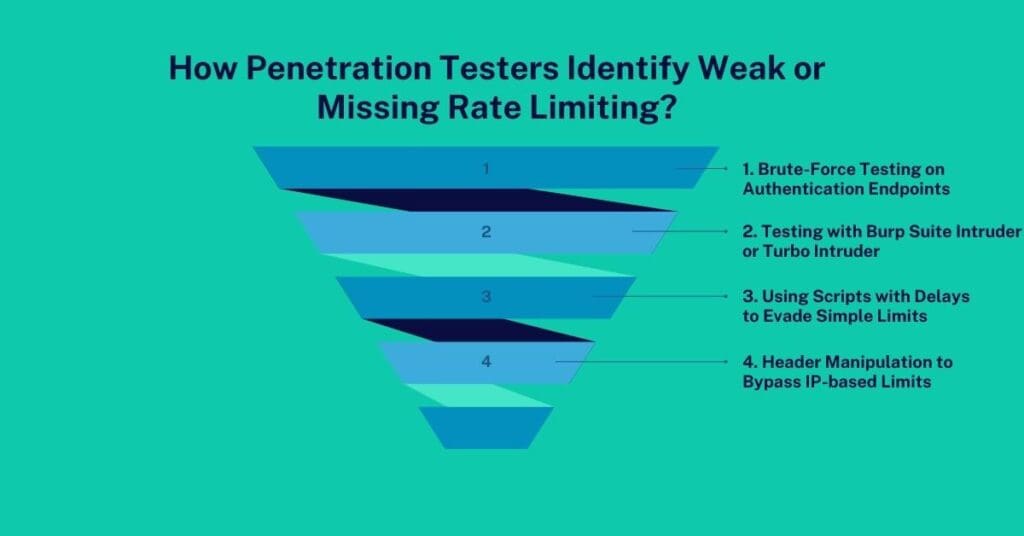
1. Brute-Force Testing on Authentication Endpoints
We script multiple requests with different credentials or OTPs to endpoints like:
- POST /api/login
- POST /api/verify-otp
- POST /api/change-password
Expected behaviour: After a few failed attempts, the API should block, throttle, or challenge the client.
Common finding: No limit or generic 200 OK responses even after 100+ attempts.
2. Testing with Burp Suite Intruder or Turbo Intruder
We send a high number of concurrent requests (e.g., 200 in a burst) and check:
- If all requests succeed (indicates no limit)
- If the server returns 429 Too Many Requests
- If tokens, OTPs, or promo codes can be brute-forced
3. Using Scripts with Delays to Evade Simple Limits
We attempt to bypass time-based windows (e.g., 5 attempts per minute) by spacing requests slightly. If rate limiting is not smartly implemented (e.g., fixed windows), this still allows enumeration.
4. Header Manipulation to Bypass IP-based Limits
We test if rate limiting is tied only to IP by modifying headers like:
- X-Forwarded-For
- X-Real-IP
Conclusion: Rate Limiting: Why its Crucial for API Security and How to Implement It
From a penetration tester’s lens, rate limiting isn’t just about traffic control, it’s a security guardrail. APIs without proper limits open themselves to account takeovers, enumeration, data scraping, and DoS.
During VAPT, testing rate limiting is a critical step that helps uncover hidden abuse opportunities. If you’re building or maintaining APIs, integrating smart rate limiting mechanisms can significantly reduce attack surfaces and improve resilience.
Need a Rate Limiting Assessment?
At CyberSapiens, we specialize in API Penetration Testing with a focus on security misconfigurations like broken rate limiting.
Let our ethical hackers evaluate your APIs before attackers do.
- 📩 Email: sales@cybersapiens.co
- 🌐 Website: cybersapiens.co
- 📞 Call: +91 6364011010 | 1300 507 668
