
Commvault Azure Breach via CVE-2025-3928: A Wake-Up Call for Cloud Security
In an alarming development for the cloud security community, Commvault, a major enterprise data backup platform, confirmed a breach in its Microsoft Azure environment caused by a zero-day vulnerability CVE-2025-3928. While Commvault stated that no customer backup data was accessed, the implications of this incident are serious and far-reaching for organisations relying on cloud infrastructure.
What Happened?
On February 20, 2025, Microsoft notified Commvault of unauthorised activity traced back to an exploited vulnerability in their Azure Web Server. The issue, later identified as CVE-2025-3928, was being used as a zero-day exploit by a nation-state threat actor.
Commvault responded swiftly by:
- Rotating affected credentials,
- Enhancing monitoring,
- Working closely with Microsoft and impacted clients.
However, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2025-3928 to its Known Exploited Vulnerabilities (KEV) catalogue, underscoring the seriousness of this threat.
Why This Breach Matters to You
Even if you are not a Commvault customer, this breach reveals critical weaknesses in cloud environments that many businesses still overlook:
- Improperly secured app registrations in Azure AD
- Stale client secrets not rotated regularly
- Lack of IP whitelisting/monitoring
- Missing Conditional Access controls
If you’re using Microsoft 365, Dynamics 365, or custom Azure apps, you’re potentially exposed to similar attack vectors.
Indicators of Compromise
Commvault and Microsoft flagged the following IPs as linked to the malicious activity. These should be blocked and monitored:
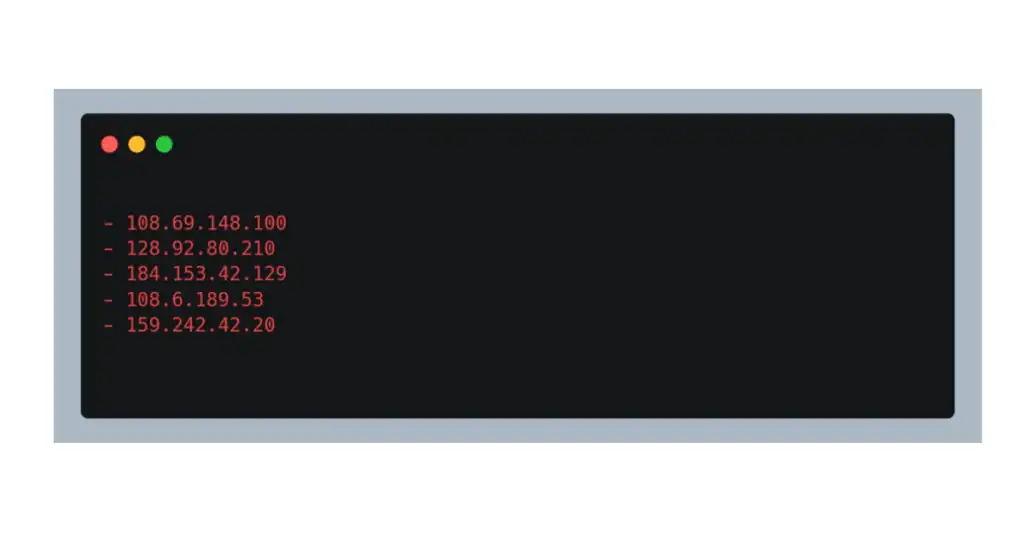
Monitoring your Azure sign-in logs and setting up alerts for unusual access attempts is no longer optional; instead, it’s essential.
What is Azure VAPT and Why Do You Need It?
Azure Vulnerability Assessment & Penetration Testing (VAPT) goes beyond basic configurations. It involves:
- Active scanning of cloud infrastructure for misconfigurations and known vulnerabilities
- Simulated attacks to test how an attacker could exploit your setup
- Secrets and key hygiene audits
- Policy review for Conditional Access and privileged identities
- Threat intelligence mapping against IPs, tactics, and patterns
How Cybersapiens Can Help
At Cybersapiens, we specialise in helping organisations secure their Azure environments before attackers can exploit them. Our Azure VAPT service includes:
- Azure AD & Conditional Access review
- Client secret rotation & key vault security
- Threat hunting for suspicious IPs
- Detection of stale or orphaned app registrations
- Remediation guidance & patch prioritisation
Need an Azure Security Audit?
At CyberSapiens, we help businesses uncover hidden vulnerabilities in their Azure environments before attackers do. Whether you’re running Microsoft 365, Azure AD, or custom apps in the cloud, we’ve got your back with expert penetration testing and actionable insights.
