
OWASP Top 10 Risks Every UAE Business Should Test with VAPT
With more and more businesses in the UAE undergoing digital transformation, web applications, cloud platforms, and digital services have become part of the business process. From banking and healthcare to government services, organizations in various industries use digital services to manage critical data and deliver an exceptional customer experience. With cybercriminals always on the lookout for vulnerabilities in web applications and enterprise systems, any vulnerability in web applications can result in data breaches and financial losses for organizations.
This is where Vulnerability Assessment and Penetration Testing come into play. This way, businesses are able to proactively deal with their security issues before they are taken advantage of by hackers. This way, businesses are able to get a clear picture of their security issues and vulnerabilities.
One of the most popular security testing frameworks is the OWASP Top 10, which is a list of the most critical web application security vulnerabilities, widely accepted across the world. This way, businesses are able to identify critical vulnerabilities in their applications, such as injection attacks, access control issues, and security configuration issues.
- What is VAPT and Why It Matters for UAE Businesses?
- Understanding the OWASP Top 10
- OWASP Top 10 Risks Every UAE Business Should Test with VAPT
- 1. Broken Access Control
- 2. Cryptographic Failures
- 3. Injection Attacks
- 4. Insecure Design
- 5. Security Misconfiguration
- 6. Vulnerable and Outdated Components
- 7. Identification and Authentication Failures
- 8. Software and Data Integrity Failures
- 9. Security Logging and Monitoring Failures
- 10. Server-Side Request Forgery (SSRF)
- How CyberSapiens Helps Businesses Identify OWASP Risks?
- Strengthening Application Security for UAE Businesses
- FAQs
What is VAPT and Why It Matters for UAE Businesses?
Vulnerability Assessment and Penetration Testing (VAPT) is a holistic approach to testing and evaluating the security posture of applications, networks, and systems. It is a combination of two testing approaches: vulnerability assessment and penetration testing.
Vulnerability assessment is primarily concerned with the identification and prioritization of security vulnerabilities in the digital infrastructure of an organization. Automated tools and security scans are used to detect vulnerabilities such as outdated software, misconfigured systems, weak encryption, and exposed services. This is more of an overview of potential vulnerabilities that may be targeted by attackers.
On the other hand, penetration testing takes it a step further by mimicking real-world cyber attacks. In penetration testing, cyber experts try to take advantage of the identified vulnerabilities to understand how such vulnerabilities can allow cyber attackers to gain unauthorized access to the system, steal sensitive information, and even cripple business operations.
In the context of UAE businesses, VAPT is significant for the protection and resilience of digital assets. With more and more UAE businesses embracing technology such as cloud computing, mobile apps, and internet services, there is also a corresponding increase in the potential entry points for cyber attackers.
By employing regular VAPT measures, UAE organizations would be able to:
- Recognize vulnerabilities before they are exploited by attackers.
- Secure sensitive customer and business information.
- Minimize financial losses and system disruptions.
- Enhance the security of applications and networks.
- Assist with compliance with various cybersecurity regulations and standards.
By testing their systems and applications, organizations would be able to minimize the risks of cyber attacks and ensure that their digital platforms remain safe and reliable.
Understanding the OWASP Top 10
OWASP Top 10 is a widely accepted list of the most critical security risks that are present in web applications. It is a list of common vulnerabilities that are exploited by hackers to gain unauthorized access to web applications and steal critical information. It is a benchmark that is followed by security experts and organizations all over the world to strengthen web applications and prevent cyber attacks.
OWASP Top 10 is a list of common vulnerabilities that are exploited by hackers to gain unauthorized access to web applications and steal critical information. It is a benchmark that is followed by security experts and organizations all over the world to strengthen web applications and prevent cyber attacks. For businesses in the UAE, it is a useful tool to identify and mitigate common security vulnerabilities in web applications and prevent cyber attacks. Many cyber attacks are carried out using common vulnerabilities in web applications, and testing applications against these vulnerabilities reduces the chances of a cyber attack.
Incorporating OWASP Top 10 testing into the VAPT process enables organizations to:
- Detect critical vulnerabilities that are commonly attacked by hackers.
- Improve the security posture of web applications during the development and deployment process.
- Detect configuration and programming errors early on.
- Improve the organization’s risk management and cybersecurity posture.
Incorporating OWASP Top 10 testing into the organization’s security testing process ensures that the organization is protecting its web applications from the most critical vulnerabilities and cyber threats.
OWASP Top 10 Risks Every UAE Business Should Test with VAPT
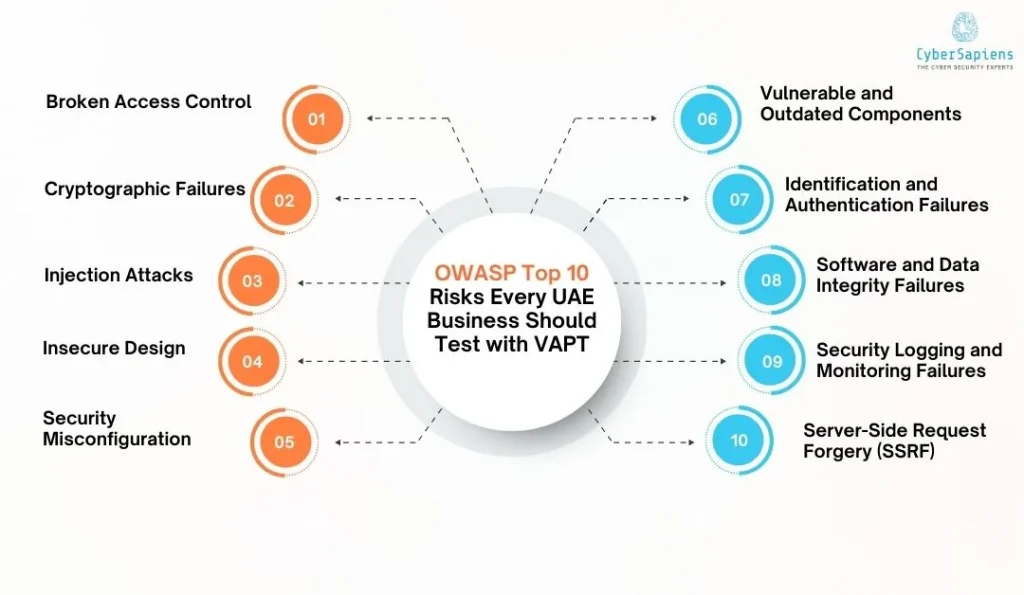
Testing applications using the OWASP Top 10 risks can help businesses identify and mitigate some of the most significant security risks and vulnerabilities exploited by attackers. By using VAPT testing, businesses can identify and mitigate risks related to these security issues.
Here are some of the major risks related to the OWASP Top 10 risks that every business in the UAE should consider:
1. Broken Access Control
Broken access control is a security risk where applications do not provide adequate control over users’ activities. This risk can allow attackers and unauthorized users to access sensitive data and perform activities without proper authorization.
Some of the activities related to broken access control are accessing another user’s account, modifying restricted data, and performing activities without authorization. VAPT testing can help identify this risk by trying to access unauthorized areas of the application without proper authorization.
2. Cryptographic Failures
Cryptographic failures occur when applications do not provide adequate security measures to protect sensitive data. This risk can allow attackers and unauthorized users to access sensitive data, which includes passwords, financial data, and personal data. VAPT testing can help identify this risk and provide adequate measures to keep sensitive data secure and protected.
3. Injection Attacks
This is a vulnerability that occurs in applications where untrusted input is sent to an interpreter in the form of a command or query. The most common example of an injection attack is SQL injection, where attackers try to obtain unauthorized data by manipulating queries in a database.
The other categories of injection attacks are command injection, LDAP injection, and XML injection. VAPT helps to identify injection attacks by checking how the application handles input data and whether proper input filtering is done.
4. Insecure Design
Insecure design is a vulnerability in an application’s architecture or development process. This is a vulnerability that is not a coding error but is a result of a poor security development practice. The examples of insecure design are a lack of threat modeling, authentication, and business logic. VAPT helps to identify potential vulnerabilities in an application’s architecture and workflow to detect possible attacks.
5. Security Misconfiguration
Security misconfigurations relate to systems, servers, and applications that are not well configured. This may include default passwords, unnecessary services running, access controls, and cloud storage. This may often serve as an easy target for attackers. VAPT testing helps identify vulnerabilities in the application by examining its configuration and testing for improperly secured areas.
6. Vulnerable and Outdated Components
Applications use third-party libraries and plugins. Attackers may use vulnerabilities in third-party plugins and libraries to access systems and data. VAPT testing helps identify outdated dependencies and plugins that may require upgrading to reduce potential vulnerabilities.
7. Identification and Authentication Failures
Authentication risks arise when the system fails to validate the user’s identification. This mainly occurs when the password policy is weak or the system lacks multi-factor authentication. When VAPT testing is done, the system’s authentication process is tested to identify any weaknesses that could be exploited by attackers to gain unauthorized access to the user’s account.
8. Software and Data Integrity Failures
This type of risk occurs when the system fails to validate the integrity of the software being updated or the data being used. This weakness could be exploited by attackers, who could introduce malware into the system’s updates. VAPT helps organizations identify how the system handles updates and the integrity of the code being used.
9. Security Logging and Monitoring Failures
If an organization does not have adequate security logging and monitoring measures in place, it can miss the opportunity to detect cyberattacks on time. This means attackers can live in the system undetected. VAPT tests examine an organization’s security logging and monitoring practices to ensure they can detect cyberattacks on time.
10. Server-Side Request Forgery (SSRF)
Server-Side Request Forgery is a cyberattack where attackers send unauthorized requests to internal systems and external services using an application. This can put internal resources, cloud resources, and metadata at risk. VAPT experts try to exploit SSRF vulnerabilities using VAPT tests to check if an application can prevent Server-Side Request Forgery.
UAE businesses can significantly enhance their application security and reduce the risk of successful cyberattacks by conducting regular VAPT tests to check for these risks identified in the OWASP Top 10 list.
How CyberSapiens Helps Businesses Identify OWASP Risks?
To identify and mitigate OWASP Top 10 vulnerabilities, a well-structured approach to security testing is necessary, and for that, experienced cybersecurity experts are a must. CyberSapiens is a cybersecurity services provider that helps businesses improve their application security by offering a comprehensive Vulnerability Assessment and Penetration Testing (VAPT) service that aims to identify critical security risks for businesses.
With a comprehensive approach to Vulnerability Assessment and Penetration Testing, businesses can identify vulnerabilities in their applications that could be exploited by attackers in the future.
The major ways in which CyberSapiens helps businesses identify OWASP risks are:
- Comprehensive VAPT Assessments: CyberSapiens delivers comprehensive vulnerability assessments and penetration tests for web applications, APIs, networks, and clouds to identify vulnerabilities according to the OWASP Top 10 list.
- OWASP-Focused Security Testing: The security testing approach is based on OWASP guidelines to identify vulnerabilities like injection attacks, access control vulnerabilities, authentication vulnerabilities, and security misconfigurations.
- Real-World Attack Simulations: Skilled ethical hackers simulate real-world attacks to test vulnerabilities in a web application and assess potential risks to business operations and data security.
- Detailed Vulnerability Reports: Businesses receive detailed reports of vulnerabilities in web applications, along with risk levels and recommendations for addressing vulnerabilities to improve overall data security.
- Remediation Guidance and Support: In addition to vulnerability assessments, businesses receive support in remediating vulnerabilities and writing secure code to prevent future risks to web applications and data security.
- Continuous Security Testing: Businesses receive continuous security testing to stay ahead of potential risks in a complex digital threat landscape and maintain a high level of data security according to OWASP guidelines.
Strengthening Application Security for UAE Businesses
As business organizations in the UAE are increasingly going digital, it is more important than ever to ensure that web applications and web platforms are secure. Cyber attackers often exploit commonly found vulnerabilities in web applications, and many of these vulnerabilities have been identified in the OWASP Top 10 list. These vulnerabilities may not be identified and mitigated in time if not addressed properly, and if not mitigated in time, it may result in serious consequences for organizations.
This is where Vulnerability Assessment and Penetration Testing (VAPT) plays a crucial role in modern cybersecurity. By conducting regular tests for vulnerabilities in web applications against the OWASP Top 10 vulnerabilities, organizations can identify vulnerabilities in their web applications and understand the impact of such vulnerabilities and how to address them effectively.
FAQs
1. Why should UAE businesses test applications against the OWASP Top 10?
Answer: Testing applications against the OWASP Top 10 helps businesses identify the most common vulnerabilities that attackers exploit. By addressing these risks early through VAPT, organizations can reduce the chances of cyberattacks and protect sensitive business and customer data.
2. How often should businesses perform VAPT testing?
Answer: Organizations should ideally conduct VAPT assessments at least once a year or whenever significant changes are made to applications, infrastructure, or systems. Many companies also perform quarterly testing to ensure continuous security.
3. Can VAPT help organizations meet compliance requirements?
Answer: Yes. Many regulatory frameworks and industry standards require regular security testing. VAPT helps organizations demonstrate that they are actively identifying and addressing security risks.
4. What types of applications should be tested for OWASP vulnerabilities?
Answer: Web applications, mobile applications, APIs, cloud-based platforms, and customer portals should all be tested for OWASP vulnerabilities to ensure they are protected against common cyber threats.
