
Anatomy of a Ransomware Attack in Healthcare: How a SOC Contained the Threat
Ransomware attacks have become a top concern in the healthcare sector. From disrupting critical systems like electronic health records (EHR) to delaying surgeries and ambulance dispatches, the consequences aren’t just financial, they can be life-threatening.
Security Operations Centres (SOCs) play a crucial role in mitigating these threats and ensuring minimal impact on patient care. In this blog, we’ll walk through a detailed Anatomy of a Ransomware Attack in Healthcare: How a SOC Contained the Threat and how the SOC effectively responded.
- Healthcare Context: Why Ransomware Hits Harder?
- Step 1: Initial Compromise – The Attack Begins Silently
- Step 2: Privilege Escalation & Lateral Movement
- Step 3: Command & Control Established
- Step 4: Ransomware Detonation
- Step 5: Full Containment
- Step 6: Root Cause Analysis & Threat Containment
- Step 7: Recovery & Restoration
- Step 8: Communication & Legal Coordination
- Step 9: Lessons Learned & Future Readiness
- Key Takeaways for Healthcare SOC Teams
- Conclusion
Healthcare Context: Why Ransomware Hits Harder?
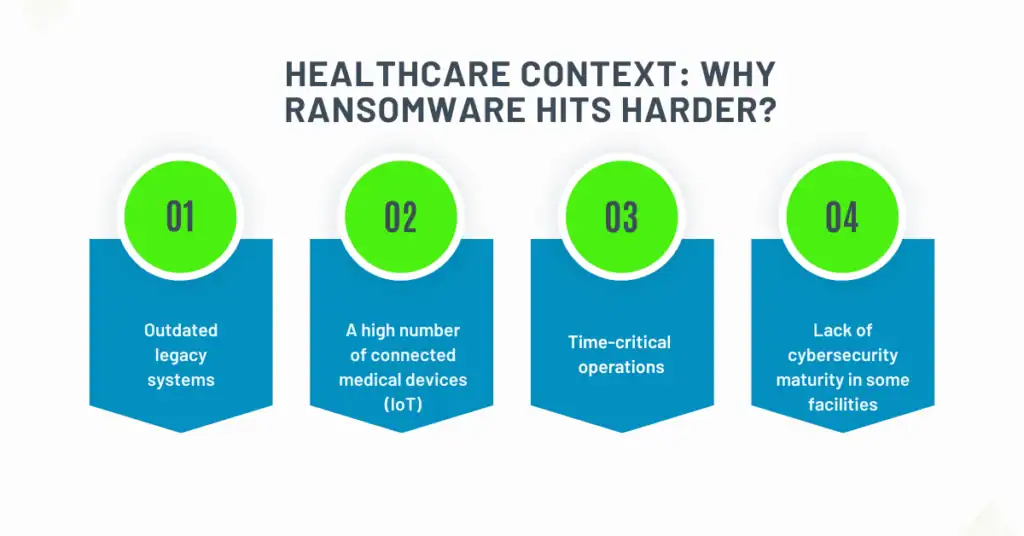
Healthcare organizations are a prime target due to:
- Outdated legacy systems
- A high number of connected medical devices (IoT)
- Time-critical operations (attackers know hospitals can’t afford downtime)
- Lack of cybersecurity maturity in some facilities
In this scenario, we examine an incident at a mid-sized private hospital group operating several clinics and a central medical center.
Step 1: Initial Compromise – The Attack Begins Silently
An employee in the radiology department receives an email that appears to come from a known medical supplier. The subject line: “New Imaging Device Specs – Q1 Update”. Attached is a malicious Excel file with embedded macros. When opened, the macro silently downloads and executes a dropper, giving the attacker initial access.
SOC Response:
- At this point, no major alert is triggered unless behavioural analytics or sandboxing is in place.
- If email gateway solutions integrate with the SOC’s SIEM, suspicious attachments can be flagged in retrospect.
- The SOC team starts correlating login attempts and endpoints that suddenly begin reaching out to unknown IPs.
Step 2: Privilege Escalation & Lateral Movement
The attacker uses credential dumping tools like Mimikatz to gain domain admin privileges. They move laterally to discover high-value targets—like EHR servers, PACS imaging systems, and the hospital’s internal file share storing patient intake forms.
SOC Response:
- SIEM and EDR systems detect abnormal logins across multiple subnets (e.g., a radiology PC querying the domain controller).
- SOC begins active threat hunting to look for signs of Pass-the-Hash and privilege escalation attempts.
- SOC triggers alerts on unusual WMI or PowerShell commands from non-admin systems.
Step 3: Command & Control Established
To maintain persistence, the attacker opens a backdoor to a Command & Control (C2) server and exfiltrates Active Directory maps and internal network diagrams.
SOC Response:
- SOC analysts detect beaconing to known malicious IPs or domains via threat intel feeds.
- DNS logs show connections to suspicious domains registered just days ago.
- The SOC updates firewall rules to block external C2 traffic and places the hospital’s public IPs on high-alert watchlist.
Step 4: Ransomware Detonation
Early one morning, at 3:12 AM, the attacker deploys Lock Bit ransomware across the hospital network. EHR systems go offline, and nurses start reporting that patient records are inaccessible.
SOC Response:
- SIEM correlation rules light up with file write/delete patterns typical of ransomware.
- SOC isolates infected endpoints using EDR agents (automated quarantine).
- Access to shared drives and clinical applications is shut down to prevent further spread.
- High-priority systems (ICU and surgical platforms) are segmented manually if automated tools fail.
Step 5: Full Containment
The attack is spreading quickly. Containment must be aggressive.
SOC Response:
- All VPN sessions are terminated.
- Domain admin accounts are disabled.
- Segmentation is enforced on patient monitoring systems, PACS servers, and nurse stations.
- The SOC issues a network-wide alert and invokes the “Code Cyber” internal response protocol.
Step 6: Root Cause Analysis & Threat Containment
Once the environment is stabilized, the SOC works with the Incident Response (IR) team to identify the source and full scope.
SOC Response:
- Forensic analysis of the initial infected machine reveals the phishing email and Excel file.
- Analysts track the attacker’s movement through the environment using SIEM and EDR logs.
- Persistence mechanisms (like scheduled tasks and registry changes) are located and removed.
Step 7: Recovery & Restoration
The hospital’s disaster recovery plan is engaged. However, the ransomware had encrypted backups stored locally—forcing reliance on offsite storage.
SOC Response:
- Verifies integrity of offsite backups before initiating restoration.
- Works with IT to clean and rebuild infected systems.
- Ensures that restored systems are fully patched and threat-free before reconnecting to the network.
- Critical care systems are prioritized—especially those in emergency and surgery departments.
Step 8: Communication & Legal Coordination
Healthcare organizations must meet compliance regulations like HIPAA (in the US) or Disha (in India), making incident disclosure and documentation essential.
SOC Response:
- Assists compliance and legal teams in identifying if patient data was exfiltrated.
- Prepares incident reports for internal audit and external regulators.
- Coordinates with law enforcement and healthcare cyber threat intelligence networks (e.g., H-ISAC).
Step 9: Lessons Learned & Future Readiness
Post-incident, the organization holds a full debrief and commits to improving its defenses.
SOC Enhancements:
- Strengthens phishing training and simulation programs.
- Implements stricter email attachment policies (e.g., disabling macros).
- Enhances network segmentation for medical devices and production workloads.
- Deploys deception technologies (honeypots) to lure future attackers.
- Refines incident response plans based on the attack timeline and bottlenecks.
Key Takeaways for Healthcare SOC Teams

1. Speed and visibility
These are critical—seconds count in stopping encryption.
2. Segmentation
This saves lives, especially when medical equipment must remain online.
3. Automated isolation
EDR and NAC tools can contain early-stage infections.
4. Regular backup validation
Off-site replication is essential.
Conclusion
In healthcare, ransomware isn’t just an IT problem—it’s a patient safety risk. The SOC’s ability to detect early signs, respond with precision, and guide recovery plays a life-saving role. By learning from past incidents and continually evolving security practices, SOCs can turn a nightmare scenario into a story of resilience and recovery.
