
Best Bug Bounty Hunting Course in Pune
As Pune continues to evolve as one of India’s major IT, engineering, and startup hubs, organisations across industries are increasingly dependent on web applications, mobile platforms, APIs, and cloud-based systems. With this rapid digital expansion, cyber threats are also growing at an alarming rate. Even companies backed by advanced security tools and experienced security teams can still overlook critical vulnerabilities.
This is where Bug Bounty Hunters, the ethical hackers of today’s digital ecosystem, play a crucial role. Bug bounty hunters help organisations uncover security weaknesses before malicious attackers can exploit them. In return, they are rewarded with cash bounties, Hall of Fame recognition, swag, reputation points, and long-term career opportunities.
As the global cybersecurity talent shortage continues to widen, the demand for skilled bug bounty hunters in Pune and across India is rising rapidly. Whether you are a student, a working professional, or someone without a technical background, bug bounty hunting offers one of the most accessible, flexible, and rewarding entry points into cybersecurity.
CyberSapiens cybersecurity experts offer the Best Bug Bounty Hunting Course in Pune, featuring specialised training in Web, API, and Mobile Application VAPT, hands-on practical labs, a guaranteed internship, and a structured, industry-aligned curriculum designed to make learners job-ready.

- What Is Bug Bounty Hunting?
- Who Can Become a Bug Hunter?
- Start Your Cybersecurity Career With CyberSapiens Bug Bounty Training in Pune
- The Bug Bounty Process
- CyberSapiens Bug Bounty Program: Web, API & Mobile VAPT Specialisation
- Why CyberSapiens Is the Best Bug Bounty Course in Pune?
- Bug Bounty: A Strong Foundation for Cybersecurity Careers
- FAQs
What Is Bug Bounty Hunting?
Bug Bounty Hunting is the ethical and authorised process of discovering and responsibly reporting security vulnerabilities in websites, mobile applications, APIs, cloud environments, and online services. Organisations launch Bug Bounty Programs—either publicly or privately—to allow ethical hackers to test their systems within legal boundaries.
In return, bug hunters earn:
- Cash rewards (bounties)
- Hall of Fame recognition
- Swag such as T-shirts, hoodies, and stickers
- Points, badges, and leaderboard rankings
Leading platforms like HackerOne, Bugcrowd, Synack, Intigriti, YesWeHack, Federacy, Google VRP, Meta Bug Bounty, and Apple Security Bounty host thousands of programs that are open to Indian hunters, including those based in Pune.
Bug bounty hunting is not illegal hacking. It is authorised, ethical, and reward-based security testing. CyberSapiens’ Bug Bounty Course in Pune teaches this ethical approach through a structured, OWASP-driven methodology, ensuring learners hunt vulnerabilities responsibly, legally, and professionally.
Who Can Become a Bug Hunter?
A common misconception is that bug bounty hunting requires a cybersecurity degree or prior IT experience. In reality, no formal degree, no prior experience, and no technical background are mandatory.
Bug bounty hunting is considered one of the most beginner-friendly paths into cybersecurity because:
- You don’t need coding skills to get started
- You don’t need an IT or engineering background
- You don’t need to be a hacker.
With curiosity, consistency, and a structured learning approach, anyone can grow into a successful bug bounty hunter.
Start Your Cybersecurity Career With CyberSapiens Bug Bounty Training in Pune
Kick-start your journey into ethical hacking and cybersecurity with a practical, beginner-friendly program focused on real-world skills. CyberSapiens equips learners with hands-on bug bounty techniques, strong VAPT fundamentals, and industry-ready experience to help them confidently step into the cybersecurity field.
CyberSapiens’ Bug Bounty Training Is Ideal For:
| Category | Description |
| Students | Fresh graduates (B.Tech / B.E / BCA / B.Sc / MCA / BVoc / M.Tech / M.E / IT) |
| Working Professionals | Individuals looking to transition into cybersecurity roles |
| Complete Beginners | Learners with no technical background or prior experience |
| IT Professionals | Those seeking practical penetration testing and security skills |
| Freelancers | Individuals aiming to earn through global bug bounty programs |
| Cybersecurity Enthusiasts | Anyone passionate about ethical hacking and vulnerability research |
The Bug Bounty Process
Bug bounty hunting is not about randomly testing websites. It follows a methodical and professional process used by top hunters worldwide, which CyberSapiens teaches in detail.
Step 1: Reconnaissance (Information Gathering)
This phase focuses on collecting publicly available information to understand the application’s structure, technologies, and exposed assets. Hunters identify subdomains, APIs, directories, servers, sensitive files, and third-party services to map the full attack surface.
Step 2: Scanning (Identifying Vulnerabilities)
After mapping the attack surface, structured scanning is performed using automated tools and manual validation techniques. This includes vulnerability detection, endpoint enumeration, open-port checks, SSL and security configuration analysis, and identifying misconfigurations.
Step 3: Exploitation (Validating Weaknesses)
In this stage, identified issues are tested ethically to confirm whether they are real and exploitable. This may include testing authentication flaws, broken access control, insecure APIs, injection vulnerabilities, and platform-specific weaknesses. Learners practise this extensively through guided labs and real-world simulations.
Step 4: Reporting (The Most Important Skill)
A vulnerability earns a reward only when reported clearly and professionally. Effective reporting includes:
- Clear vulnerability description
- Proof-of-Concept (PoC)
- Step-by-step reproduction steps
- Screenshots or video evidence
- Impact assessment with CVSS scoring
- Mitigation recommendations
CyberSapiens trains learners to create VAPT-grade reports trusted by security teams globally.
Step 5: Rewards
Once validated, organisations issue rewards based on severity and impact:
- Low severity: ₹1,000 – ₹5,000
- Medium severity: ₹5,000 – ₹20,000
- High severity: ₹30,000 – ₹3,00,000+
- Critical vulnerabilities: ₹10 lakhs – ₹50 lakhs+
Beyond monetary rewards, hunters may also receive Hall of Fame recognition, swag kits, achievement badges, and leaderboard rankings. CyberSapiens also supports earn-while-you-learn opportunities, allowing learners to practise in real environments.
CyberSapiens Bug Bounty Program: Web, API & Mobile VAPT Specialisation

CyberSapiens integrates bug bounty hunting into a complete professional VAPT framework, ensuring learners gain real-world, industry-relevant skills.
1. Web Application Penetration Testing
Learners gain deep expertise in identifying and exploiting vulnerabilities in modern web applications, covering:
- OWASP Top 10 methodologies
- Manual exploitation techniques
- Live testing simulations
- Detection of advanced business logic flaws
Training includes extensive hands-on use of tools such as Nmap, Burp Suite, OWASP ZAP, Metasploit Framework, Nuclei, SQLmap, FFUF, Dirsearch, Gobuster, Wpscan, CMSeek, SecurityHeaders, BXSSHunter, Kali Linux, Cookie Editor, FoxyProxy, MxToolbox, Subfinder, Paramspider, Waybackurls, Katana, Httpx, Wappalyzer, Shodan.io, Censys, Githubleaks, GHDB, Recon-ng, and Dnsrecon.
2. API Security Testing
Learners are trained to:
- Apply the OWASP API Top 10 frameworks
- Identify authentication and token-based issues
- Detect broken access control and authorization flaws
- Perform API reconnaissance and endpoint testing
- Analyse advanced API logic vulnerabilities
3. Mobile Application Penetration Testing (Android & iOS)
The mobile VAPT specialisation covers:
- Reverse engineering using professional tools
- Dynamic analysis and runtime manipulation
- API traffic interception and analysis
- Root and jailbreak detection bypass
- Assessment of insecure storage and configurations
This end-to-end training equips learners with the practical skills required to secure the mobile ecosystems powering modern digital businesses.
Why CyberSapiens Is the Best Bug Bounty Course in Pune?
- Comprehensive 6-Month Structured Program: The program is carefully designed to take learners from core cybersecurity fundamentals to advanced bug bounty and VAPT techniques over six months. Each phase builds progressively, ensuring strong conceptual clarity, practical depth, and real-world readiness rather than surface-level learning.
- Mentor-Led Training by Active VAPT Professionals: All sessions are delivered by experienced VAPT practitioners who actively work in the cybersecurity industry. Learners benefit from real-world insights, current attack trends, practical methodologies, and firsthand exposure to how professional security teams operate.
- Specialisation in Web, API & Mobile Application VAPT: Instead of focusing only on basic bug bounty concepts, the course offers deep specialisation in web, API, and mobile application penetration testing. This enables learners to test modern application architectures using industry-recognised frameworks and techniques.
- Hands-On Labs and Real-World Case Studies: Every module includes guided practical labs, simulations, and real-world scenarios. Learners practise identifying, exploiting, and reporting vulnerabilities in controlled environments that closely mirror real production systems.
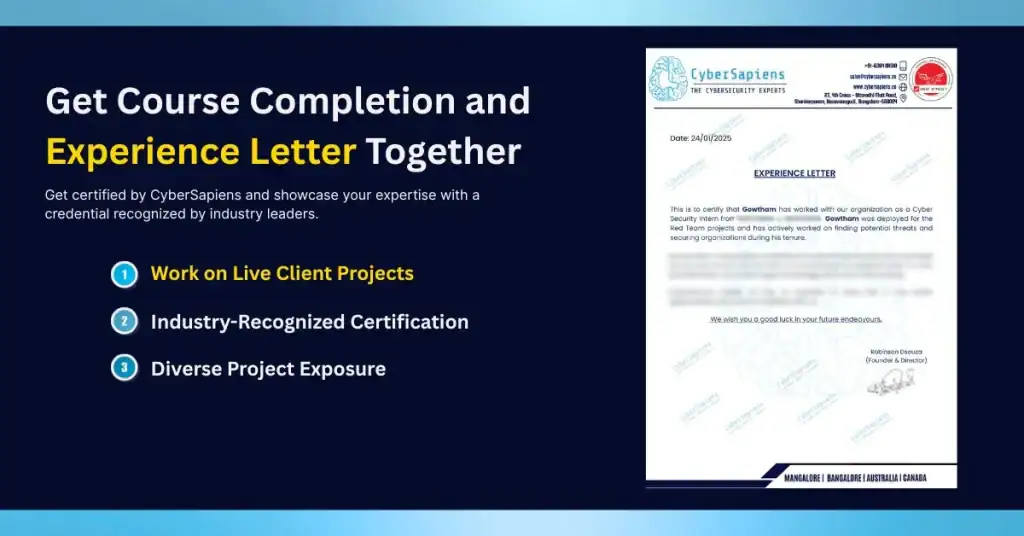
- Guaranteed Internship with Verified Experience Letter: Participants work on real cybersecurity projects during the internship phase, gaining valuable industry exposure. Upon completion, learners receive a verified experience letter that strengthens their resume and improves employability.
- Placement Assistance and Career Mentoring: Dedicated career support is provided through resume building, mock interviews, soft-skill development, and one-on-one mentoring. This helps learners confidently prepare for job roles in cybersecurity and penetration testing.
- Access to 1000+ Cybersecurity Tools and Lifetime Recordings: Learners gain hands-on exposure to an extensive range of tools used by ethical hackers and VAPT teams worldwide.

Bug Bounty: A Strong Foundation for Cybersecurity Careers
Bug bounty hunting builds essential cybersecurity skills such as analytical thinking, research ability, patience, and problem-solving. With continuous practice and real-world exposure, learners develop strong technical and investigative capabilities.
CyberSapiens strengthens this growth through a structured, mentor-led, and internship-integrated learning environment, transforming beginners into industry-ready bug bounty hunters prepared for global opportunities.
If you are serious about starting your career as a Bug Bounty Hunter or Ethical Hacker, enrolling in the Best Bug Bounty Hunting Course in Pune at CyberSapiens is one of the most impactful steps you can take toward a successful future.
FAQs
1. Can beginners join the CyberSapiens Bug Bounty Course?
Answer: Yes. No technical background is required.
2. Will I get a job after completing this course?
Answer: Yes. The program includes Web, API, and Mobile VAPT specialisation, along with internship and placement assistance.
3. Do I need coding skills to start bug bounty hunting?
Answer: Not initially. Basic scripting becomes helpful as you progress.
4. What is the duration of the course?
Answer: The program includes 6 months of comprehensive training, followed by a hands-on internship for real-world experience.
