
BOLA Vulnerability: How Attackers Exploit It and How to Prevent It
In the world of API security, one vulnerability that consistently stands out due to its potential impact is BOLA (Broken Object Level Authorization). This vulnerability occurs when an API improperly grants access to a resource or data that should be restricted based on the user’s access level . Exploiting this can lead to unauthorized access, data breaches, and severe security compromises API.
Here in this article, we are going to discuss the topic of BOLA Vulnerability: How Attackers Exploit It and How to Prevent It
What is BOLA Vulnerability?
BOLA happens when an API fails to properly check the authorization of a user trying to access a specific resource. If the system doesn’t confirm whether the user is authorized to interact with the resource they are requesting, they can potentially access data or functionality that they shouldn’t.
How Attackers Exploit BOLA Vulnerability?
Attackers can take advantage of BOLA vulnerabilities in several ways:
1. Unrestricted Access
Attackers manipulate API endpoints to gain access to objects or data tied to other users, bypassing the authorization checks.
2. Privilege Escalation
By altering the request parameters, attackers can escalate their privileges and gain unauthorized access to sensitive resources.
3. Data Theft
Once an attacker successfully exploits BOLA, they can access, steal, and misuse sensitive data such as personal information, financial details, or private business data.
4. Undetected Access
Often, BOLA vulnerabilities go undetected until significant damage is done, making it crucial to monitor API security rigorously.
How to Identify BOLA Vulnerabilities in an API
Step 1 — Detect a Critical Parameter in an API Endpoint
A critical parameter is an ID number or name in an API request that tells the server which piece of information to fetch. If this parameter is an ID, it usually belongs to a specific user, account, order, or file.
Examples of critical parameters are:
- userId
- accountId
- orderId
- fileId
- recordId
Example API Request in Postman:
Imagine an API call you use to view your own account details.
GET https://jsonplaceholder.typicode.com/users/1 Here “1” is the critical parameter (users/1)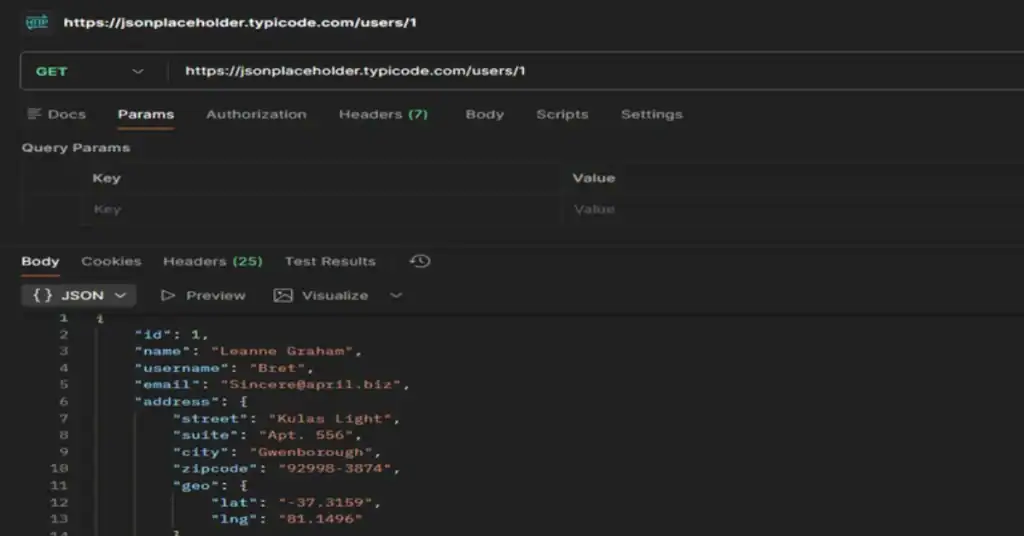
Step 2: Change the Critical Parameter
The next step is to test the API’s security by changing the critical parameter to a different value. You are pretending to be another user to see if the system will let you look at their private data.
For example, if your ID is 1 or 1001 you would change it to another likely IDs like 2 or1002
GET https://jsonplaceholder.typicode.com/users/1 -> GET https://jsonplaceholder.typicode.com/users/2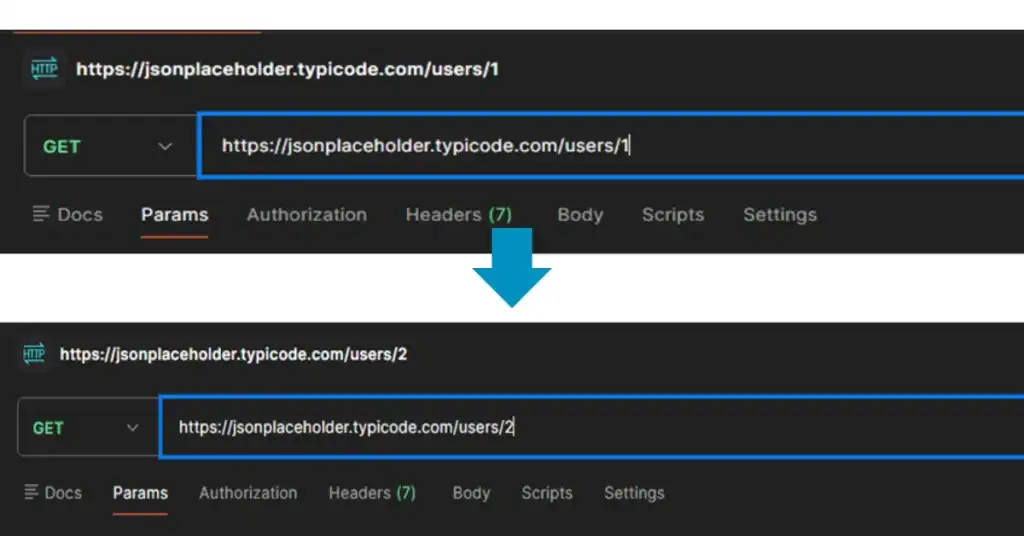
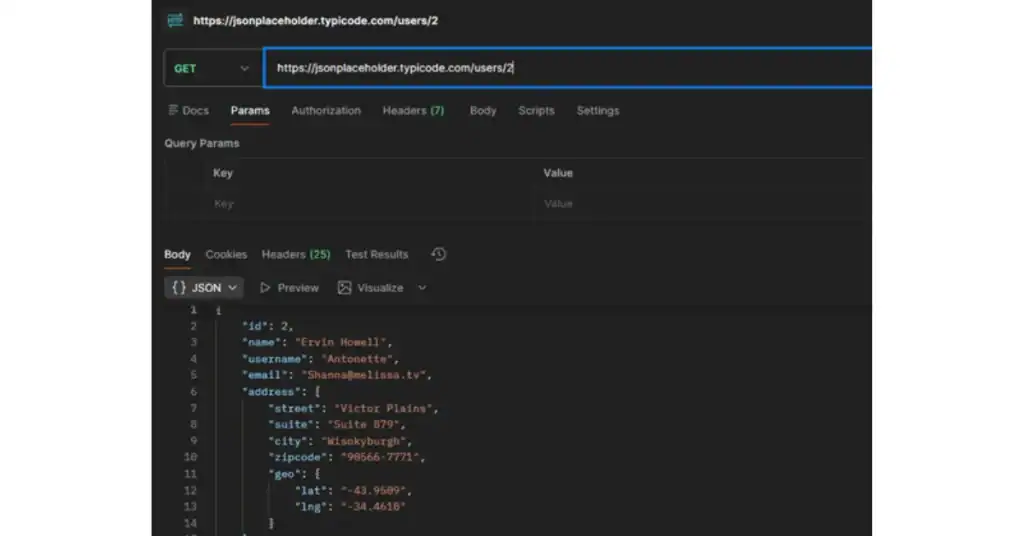
Step 3: Send the modified API request
After clicking Send, look closely at the data that comes back in the response panel.
BOLA Vulnerability Detected: If the response returns data belonging to another user (in this case, user/2 details) or exposes other users’ sensitive information, you have found a BOLA vulnerability. The system failed to check if you (user/1) have permission to view their data (user/2).
Postman tool Download Link
Download Postman: https://www.postman.com/downloads/
How to Prevent BOLA Vulnerabilities?
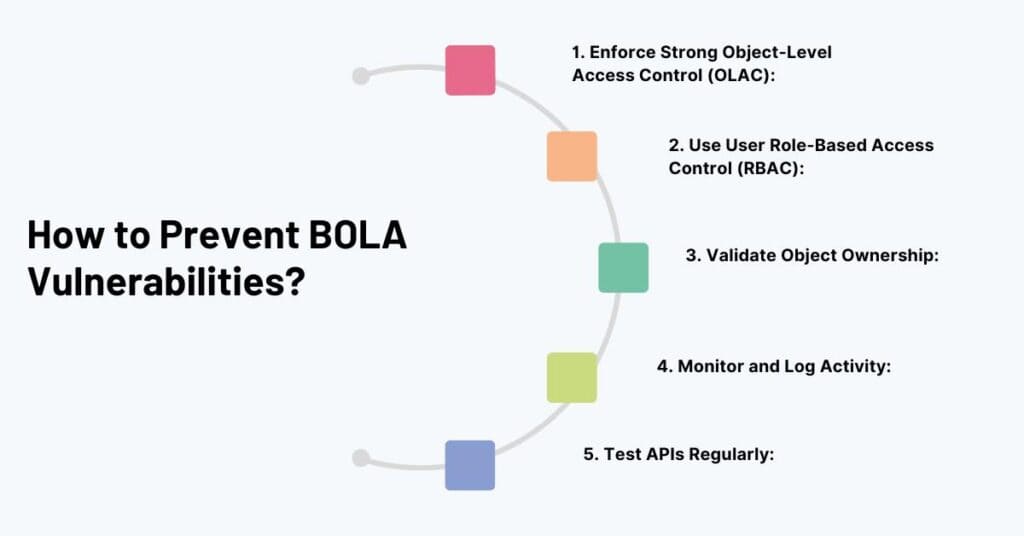
To mitigate the risk of BOLA vulnerabilities, organizations need to implement robust authorization mechanisms at the object level:
1. Enforce Strong Object-Level Access Control (OLAC):
Ensure that each request is validated against the user’s permissions before accessing the resource. An attacker should never be able to change parameters in the request to view unauthorized data.
2. Use User Role-Based Access Control (RBAC):
Define user roles and ensure that only users with specific roles can access particular resources.
3. Validate Object Ownership:
Verify that the authenticated user owns or is authorized to access the resource being requested, especially when the resource is tied to a user ID or other unique identifier.
4. Monitor and Log Activity:
Track API requests to identify any abnormal behaviour, such as unauthorized attempts to access objects.
5. Test APIs Regularly:
Perform regular API VAPT (Vulnerability Assessment and Penetration Testing) to identify and patch potential BOLA vulnerabilities before they can be exploited.
Conclusion: BOLA Vulnerability: How Attackers Exploit It and How to Prevent It
BOLA vulnerabilities can cause serious harm to businesses, leading to data breaches and loss of trust. However, by implementing proper access control mechanisms, validating user authorization at the object level, and regularly testing APIs, organizations can significantly reduce the risk of exploitation.
At CyberSapiens we specialize in API Vulnerability Assessment and Penetration Testing (API VAPT) services. Our team can help you identify BOLA and other security flaws in your API, ensuring that your sensitive data and resources remain protected. Don’t wait for a breach to happen. Let us help you strengthen your API security today.
