Common Reasons Why SaaS Companies Fail Their SOC 2 Type 2 Audit?
For SaaS companies, SOC 2 Type II has become a critical trust requirement, especially when selling to enterprise customers. Unlike SOC 2 Type I, which evaluates control design at a single point in time, SOC 2 Type II assesses whether controls operate effectively over an extended period (typically 6–12 months). This ongoing evaluation is where many SaaS companies struggle and ultimately fail.
SOC 2 Type II failures rarely happen because companies lack security policies. Instead, they occur due to inconsistent control execution, missing evidence, weak operational discipline, and a lack of continuous oversight throughout the audit period. Missed access reviews, incomplete logs, untracked changes, or gaps in vulnerability management can quickly lead to audit exceptions that impact the final report.
For fast-growing SaaS organizations, maintaining audit-ready controls while scaling teams, infrastructure, and product releases is a real challenge. Treating SOC 2 as a one-time compliance project rather than an ongoing operational process is one of the most common mistakes.
Understanding SOC 2 Type II Audit Requirements
To understand why SaaS companies fail SOC 2 Type II audits, it’s important to first understand what auditors are actually evaluating. SOC 2 Type II is not a point-in-time assessment; it measures whether your controls are designed correctly and consistently operating over a defined period, usually 6 to 12 months.
What SOC 2 Type II Really Tests?
- Control Design: Whether security, availability, and confidentiality controls are appropriately designed to meet the selected Trust Services Criteria.
- Operating Effectiveness Over Time: Auditors examine whether those controls were followed every time they were required throughout the audit period, not just during audit preparation.
- Consistency and Evidence: Every control must be supported by dated, complete, and traceable evidence covering the entire audit window.
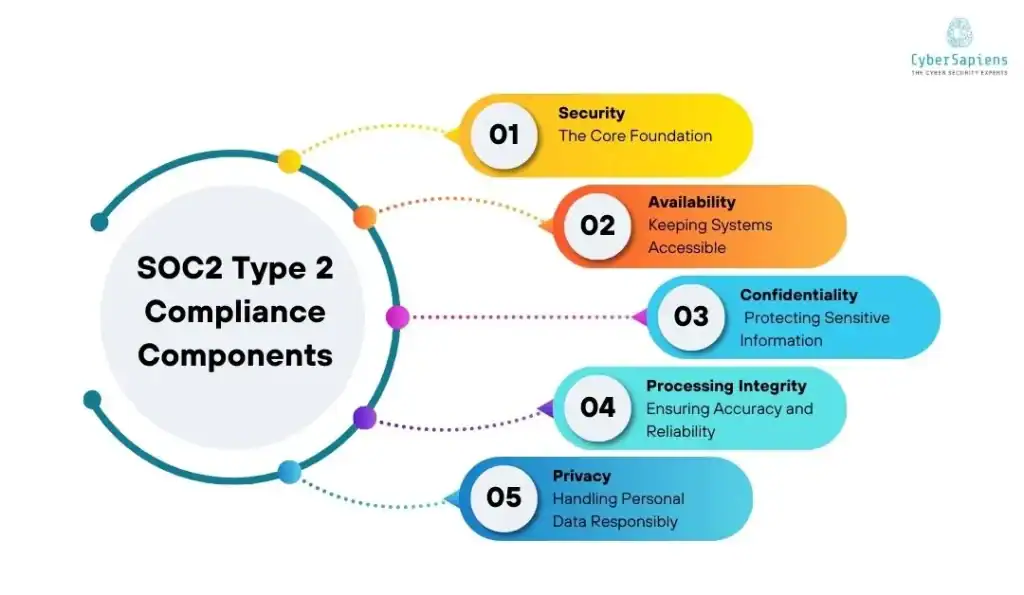
Trust Services Criteria in Scope
SOC 2 Type II audits are based on the Trust Services Criteria (TSC).
- Security (mandatory for all SOC 2 reports)
- Availability
- Confidentiality
- Processing Integrity
- Privacy
SaaS companies typically include Security and Availability, with others added based on customer and data requirements.
Why SaaS Companies Struggle with Type II?
- Rapid infrastructure and team changes during the audit period.
- Manual processes that break as the company scales.
- Lack of centralized evidence tracking.
- Controls designed but not operationalized in daily workflows.
Auditors do not accept explanations or intent, only evidence. A single missed access review, incomplete log, or undocumented change can result in an exception.
Common Reasons Why SaaS Companies Fail Their SOC 2 Type II Audit?
SOC 2 Type II failures rarely come from a single major issue. Instead, they are usually the result of multiple small gaps that persist over the audit period. Below are the most common reasons SaaS companies fail their SOC 2 Type II audits, explained together in one consolidated view.
1. Inconsistent Control Execution Over Time: Controls may be well-designed, but they are not followed consistently throughout the 6–12 month audit period. Missed access reviews, delayed approvals, or skipped security checks quickly lead to audit exceptions.
2. Poor Evidence Collection and Documentation: SaaS companies often fail to collect and store evidence continuously. Missing screenshots, logs, timestamps, or approvals, even for a single month, can result in failed control testing.
3. Weak Access Control and User Management: Excessive privileges, lack of periodic access reviews, and poor joiner–mover–leaver processes are among the most frequent audit findings in SOC 2 Type II reports.
4. No Regular Vulnerability Management or VAPT: Many organizations perform vulnerability assessments or penetration tests only once. SOC 2 Type II expects ongoing vulnerability management, remediation tracking, and re-testing evidence.
5. Ineffective Incident Response and Monitoring: Incident response plans exist on paper but are not tested or followed. Lack of incident logs, alerts, or tabletop exercises weakens audit confidence.
6. Third-Party and Cloud Vendor Risks Ignored: SaaS companies often rely heavily on cloud providers and third-party services but fail to perform vendor risk assessments or collect security assurances during the audit period.
7. Security Awareness and Training Gaps: Employees are unaware of security responsibilities, phishing risks, or reporting procedures. Missing training records also create audit evidence gaps.
8. Poor Change Management and SDLC Controls: Untracked code changes, missing approvals, and lack of testing evidence in CI/CD pipelines frequently result in control failures during audits.
9. Lack of Management Oversight and Governance: SOC 2 requires management involvement. Missing risk reviews, security discussions, or formal oversight weaken control effectiveness and audit outcomes.
10. Treating SOC 2 as a One-Time Project: The most common root cause: organizations prepare just before the audit instead of maintaining continuous compliance throughout the audit period.
How CyberSapiens Helps SaaS Companies Pass SOC 2 Type II?
Passing a SOC 2 Type II audit is challenging for SaaS companies because it evaluates control effectiveness over time, not just control design. Fast product releases, changing infrastructure, and growing teams often introduce gaps that auditors quickly identify. Cybersecurity experts at CyberSapiens help SaaS organizations overcome these challenges by building a continuous, audit-ready security program that operates reliably throughout the entire audit period.
End-to-End SOC 2 Type II Support for SaaS Companies
1. SOC 2 Type II Readiness and Gap Assessment
CyberSapiens begins by evaluating existing security controls against the selected Trust Services Criteria. This assessment highlights weaknesses in control execution, documentation, and evidence management, allowing issues to be fixed before the audit window begins.
2. SaaS-Specific Control Design and Operationalization
Controls are tailored to SaaS environments, including cloud infrastructure, CI/CD pipelines, APIs, and customer data platforms. CyberSapiens ensures controls are embedded into daily operations so they are executed consistently, not just during audit preparation.
3. Continuous Evidence Collection and Audit Traceability
One of the biggest SOC 2 Type II failure points is missing evidence. CyberSapiens helps establish structured evidence tracking processes so logs, approvals, screenshots, and reports are captured continuously across the entire 6–12 month audit period.
4. Access Control and Identity Management Strengthening
CyberSapiens supports the implementation of strong joiner–mover–leaver processes, role-based access control, privileged access reviews, and periodic access certifications, areas heavily scrutinized by SOC 2 auditors.
5. Vulnerability Management and VAPT Integration
Regular vulnerability assessments and penetration testing are scheduled, tracked, and mapped to SOC 2 requirements. Remediation and re-testing evidence is maintained to demonstrate ongoing risk management.
6. Incident Response and Security Monitoring Readiness
Incident response plans are not only documented but also tested through simulations and tabletop exercises. Monitoring, alerting, and incident logging processes are aligned with SOC 2 expectations.
7. Third-Party and Cloud Vendor Risk Management
CyberSapiens helps SaaS companies identify critical vendors, perform risk assessments, collect security assurances, and maintain vendor oversight evidence throughout the audit period.
8. Security Awareness and Employee Training Programs
Role-based security awareness training and phishing simulations are implemented with clear attendance and completion records, ensuring both effectiveness and audit evidence.
9. Management Oversight and Governance Support
CyberSapiens assists in establishing formal management reviews, risk discussions, and governance documentation to demonstrate leadership involvement and accountability.
10. Ongoing Compliance Support Throughout the Type II Period
Instead of last-minute audit preparation, CyberSapiens provides continuous guidance, periodic check-ins, and control reviews to ensure the organization remains audit-ready until the final auditor evaluation.
By combining deep SOC 2 expertise, SaaS-specific security operations, and continuous compliance support, CyberSapiens helps SaaS companies pass SOC 2 Type II audits with confidence, while continuing to scale securely and efficiently.
Turning SOC 2 Type II into a Competitive Advantage
SOC 2 Type II does not fail SaaS companies because of missing intent; it fails them due to inconsistent execution, weak evidence, and lack of continuous oversight. When treated as a one-time audit exercise, even well-designed controls can break down over the audit period.
A successful SOC 2 Type II outcome requires embedding security controls into everyday operations, maintaining continuous evidence, and aligning technical, operational, and governance practices throughout the year. When done correctly, SOC 2 becomes more than a compliance requirement; it becomes a signal of reliability and trust to enterprise customers.
With its SaaS-focused SOC 2 expertise, technical validation, and continuous compliance support, CyberSapiens helps organizations move from reactive audit preparation to sustained audit readiness. By turning SOC 2 Type II into a living security program, CyberSapiens enables SaaS companies to pass audits confidently while accelerating growth and customer trust.
FAQs: Common Reasons Why SaaS Companies Fail Their SOC 2 Type 2 Audit
1. What is the most common SOC 2 Type II audit finding?
Answer: Missing or incomplete evidence, such as skipped access reviews, missing logs, or undocumented approvals, is one of the most common findings.
2. How long does a SOC 2 Type II audit take?
Answer: The audit period typically lasts 6–12 months, followed by the auditor’s testing and reporting phase.
3. Do SaaS companies need VAPT for SOC 2 Type II?
Answer: SOC 2 does not explicitly mandate VAPT, but auditors strongly expect regular vulnerability assessments, penetration testing, and remediation evidence.
4. How early should SaaS companies prepare for SOC 2 Type II?
Answer: Preparation should begin before the audit period starts so controls and evidence processes operate consistently throughout the audit window.