
PCI DSS Compliance and Audit Service Providers in Canada
As digital payments continue to grow across Canada’s retail, e-commerce, hospitality, and financial sectors, safeguarding cardholder information has become a top priority for businesses of all sizes. PCI DSS (Payment Card Industry Data Security Standard) provides a global security benchmark that helps organisations secure payment environments, minimize fraud risks, and ensure customer confidence in every transaction.
For Canadian businesses that store, process, or transmit payment card data, PCI DSS compliance is more than a regulatory expectation—it is a critical commitment to protecting sensitive financial information amid rising cyberattacks and evolving digital-payment adoption.
Choosing the right PCI DSS compliance and audit service provider in Canada can streamline your compliance journey, helping your organisation identify security gaps, implement necessary controls, and maintain ongoing certification. This blog explores what PCI DSS means for Canadian organisations and how specialised providers can support end-to-end compliance.
What is PCI DSS Compliance?
PCI DSS Compliance means adhering to the global security framework developed by major card brands: Visa, Mastercard, Discover, American Express, and JCB to protect cardholder data. Any Canadian business that handles payment card information must comply with PCI DSS to ensure secure data handling, prevent fraud, and reduce the risk of breaches.
In simpler terms, PCI DSS compliance involves implementing required security safeguards, including: data encryption, network security and segmentation, access controls, vulnerability management, monitoring, testing, and regular assessments. Compliance helps strengthen customer trust, avoid penalties from payment processors or card brands, and support secure digital business operations.
Understanding PCI DSS Requirements
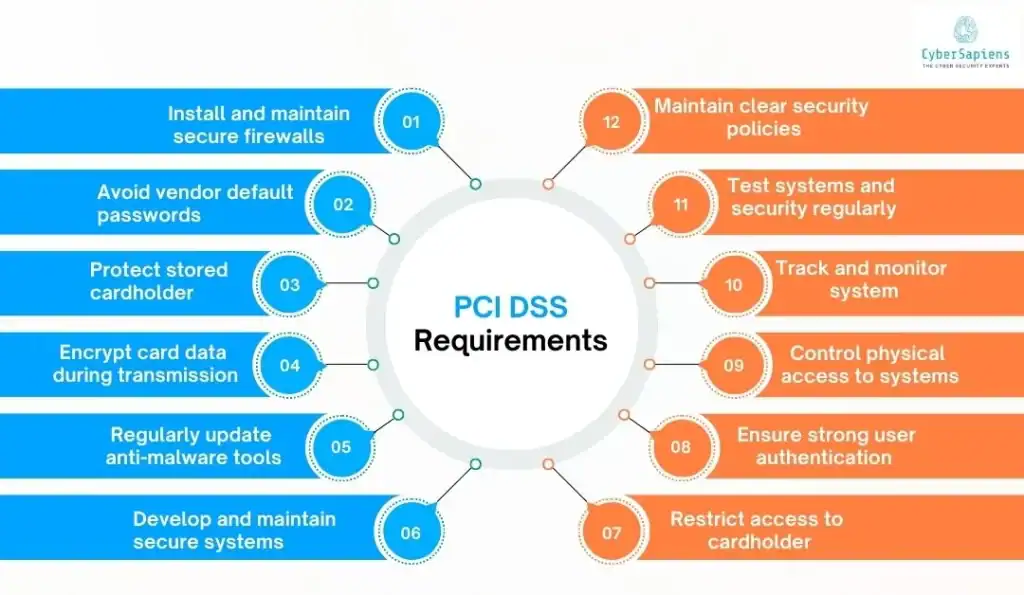
PCI DSS consists of 12 core requirements that help organisations secure cardholder data throughout its lifecycle. These requirements guide businesses in hardening systems, preventing unauthorized access, and detecting suspicious activity early.
The 12 PCI DSS Requirements
- Install and maintain secure firewalls to protect cardholder environments: Firewalls act as a critical security barrier between trusted internal networks and untrusted external networks, such as the internet. To protect cardholder data environments (CDE), organisations must deploy well-configured firewalls that control incoming and outgoing traffic based on approved security rules. This includes defining permitted services, ports, and protocols while blocking unnecessary or risky communication paths.
- Avoid vendor default passwords and configurations: Default credentials and factory configurations are widely known and easily exploitable by cybercriminals. Organisations must replace default usernames, passwords, certificates, and configuration settings before deploying systems into production.
- Protect stored cardholder data with strong cryptography: When cardholder data must be retained, it should be secured using strong cryptographic methods such as encryption, tokenization, hashing, and truncation. Sensitive authentication data, such as full magnetic stripe or CVV codes, should never be stored after authorization.
- Encrypt card data during transmission across public networks: Cardholder data transmitted over public or unsecured networks, such as the internet, wireless connections, or satellite links, must be encrypted using industry-recognized protocols like TLS 1.2 or above.
- Use and update anti-malware protections regularly: Anti-malware tools such as antivirus solutions, endpoint security platforms, and threat-detection agents must be installed on systems commonly targeted by malicious software. These protections should be enabled continuously, updated with the latest signatures, and configured to scan automatically.
- Develop and maintain secure systems through patches & secure coding: Security vulnerabilities in software and operating systems can be exploited if not addressed promptly. Organisations must implement a structured patch-management process to deploy updates within vendor-recommended timeframes. Developers should also follow secure coding practices to prevent common attack vectors like SQL injection, XSS, command injection, and insecure deserialization.
- Restrict access to cardholder data based on job responsibilities: Access to sensitive payment data should only be granted to individuals whose roles require it to perform business functions. Role-based access control (RBAC) ensures that access is both minimal and necessary.
- Ensure strong authentication and identity controls: Every person accessing systems in the cardholder data environment must have a unique user ID to maintain traceability. Strong authentication, such as multi-factor authentication (MFA), should be enforced for administrative and remote access to ensure credentials alone are not enough for system entry.
- Control physical access to systems with sensitive data: Physical protections safeguard servers, storage media, workstations, and paper records containing cardholder data from theft, tampering, or unauthorized viewing. Organisations must secure facilities using locked data centers, access cards, surveillance systems, visitor logs, and restricted entry zones.
- Monitor and log system access for early breach detection: Continuous monitoring and logging of system events allow organisations to track who accessed systems, what actions were taken, and when changes occurred. Centralized logging, SIEM solutions, and alert mechanisms help detect unauthorized activities and potential breaches before significant damage occurs.
- Regularly test systems through scans and penetration testing: Security testing validates whether implemented defenses are functioning as intended. Organisations must conduct quarterly vulnerability scans, internal and external tests, and annual penetration tests to identify exploitable weaknesses before attackers do.
- Maintain organizational security policies and training: Policies define expected security behavior, responsibilities, and procedures for safeguarding cardholder data. Organisations must develop and regularly update security policies that address access control, incident response, acceptable use, and data handling.
Why Businesses in Canada Need PCI DSS Compliance?
With digital transactions accelerating across Canada, especially through tap-to-pay, e-commerce, and mobile payments, breach risks have expanded. PCI DSS offers structured safeguards that reinforce payment trust and operational resilience.
- Protects cardholder data from theft and cyberattacks.
- Builds customer trust through secure payment processing.
- Reduces breach-related financial and legal risks.
- Helps avoid penalties from banks, processors, and card brands.
- Strengthens internal security posture and reduces vulnerabilities.
- Aligns with Canadian privacy and data-protection expectations, including PIPEDA.
- Supports compliance for industries like retail, hospitality, fintech, healthcare, and transportation.
Whether you operate a nationwide retail chain or a growing online store, PCI DSS safeguards help protect payment operations in Canada’s highly competitive market.
Benefits of Partnering With the Right Audit Service Provider
Working with the right PCI DSS Compliance and Audit Service Providers in Canada can simplify compliance and help organisations mature their security practices.
- Accelerates compliance with expert guidance and interpretation: Experts simplify complex PCI DSS requirements, helping organisations reach compliance faster and with fewer errors.
- Identifies critical vulnerabilities and security gaps: Thorough assessments uncover weaknesses that put cardholder data at risk, enabling targeted fixes.
- Supports remediation planning and implementation: Provides clear action plans and hands-on support to address security gaps and meet compliance standards.
- Streamlines documentation and evidence collection: Organizes required records and evidence, reducing administrative workload and ensuring audit readiness.
- Prepares teams for formal QSA assessments: Readiness sessions and mock audits build confidence and ensure teams understand expectations before the official assessment.
- Strengthens security beyond minimum requirements: Recommendations go beyond compliance, enhancing overall security posture and resilience against modern threats.
- Minimizes risk of penalties and card-data breaches: Strong compliance reduces the likelihood of costly breaches, fines, and disruptions to payment operations.
- Offers continuous support to maintain compliance year-round: Ongoing monitoring, reporting, and updates help businesses stay compliant between audits and adapt to changes.
Top 5 PCI DSS Compliance and Audit Service Providers in Canada

1. Cybersapiens
Cybersapiens provides end-to-end PCI DSS consulting, compliance readiness, gap assessments, remediation support, and certification assistance tailored for Canadian businesses handling cardholder data.
Cybersapiens Process for PCI DSS Compliance in Canada
1. Initial Scoping & Gap Analysis
This phase establishes a clear understanding of how and where cardholder data exists within your organisation. The provider maps all storage, processing, and transmission points across systems, applications, and workflows to define an accurate and manageable scope for PCI DSS compliance.
2. Compliance Roadmap & Planning
Based on the findings from the gap analysis, a structured and prioritized compliance roadmap is created. This roadmap outlines the steps required to meet PCI DSS requirements, focusing on the most critical remediation activities first, such as securing network components, refining access policies, and addressing documentation gaps.
3. Implementation Support
During this phase, the provider works closely with internal teams to implement the required controls and system changes. This includes deploying technical safeguards such as network segmentation to isolate the CDE, enforcing access management policies, enabling encryption for sensitive data, and configuring monitoring systems for visibility and alerting.
4. Internal Testing & Validation
Before undergoing an official PCI DSS assessment, internal testing is performed to verify that implemented controls are functioning as intended. This includes internal and external vulnerability scans, configuration reviews, and simulated assessments to validate compliance readiness.
5. Audit & Reporting
Once systems and processes meet PCI DSS requirements, the provider assists in preparing for the formal audit conducted by a Qualified Security Assessor (QSA). This includes compiling and reviewing documentation, evidence, policies, configuration records, network diagrams, and logs to ensure completeness and alignment with PCI requirements.
6. Post-Assessment & Continuous Compliance
PCI DSS compliance is ongoing, not a one-time achievement. After certification, the provider continues to assist with maintaining compliance through continuous monitoring, policy updates, periodic access reviews, and system evaluations.
Clients Served by CyberSapiens





2. Control Gap
A leading PCI DSS Qualified Security Assessor (QSA) firm in Canada offering assessments, advisory services, scope reduction strategies, and forensic investigations related to card-data security.
3. Trustwave Canada
Global cybersecurity provider with Canadian presence, offering PCI DSS assessments, managed security services, penetration testing, and continuous compliance monitoring.
4. Bulletproof
Canadian cybersecurity consulting provider offering PCI DSS readiness, assessment support, vulnerability management, penetration testing, and compliance advisory for regulated industries.
5. ISA Cybersecurity
A Canadian cybersecurity specialist delivering PCI DSS consulting, risk assessments, managed security, and audit preparation tailored to Canadian regulatory environments.
Strengthening Payment Security with PCI DSS Compliance
Achieving and maintaining PCI DSS compliance is crucial for Canadian businesses that handle cardholder data. It reinforces secure payment operations, reduces the likelihood of cyberattacks, and builds long-term customer trust.
With the growth of digital transactions and increasingly sophisticated threats, partnering with the right PCI DSS Compliance and Audit Service Provider in Canada ensures your organisation not only meets industry expectations but also strengthens overall security maturity.
By following a structured approach like the one adopted by Cybersapiens, businesses can confidently progress from assessment to certification and ongoing compliance, turning PCI DSS into a continuous security advantage rather than a one-time requirement.
FAQs
1. Who needs PCI DSS compliance in Canada?
Answer: Any business that stores, processes, or transmits cardholder data, including retailers, e-commerce businesses, payment processors, hospitality providers, healthcare services, and fintech companies.
2. How often should PCI DSS assessments be conducted?
Answer: Annual assessments and quarterly vulnerability scans are required to maintain compliance.
3. What are the penalties for non-compliance?
Answer: Financial penalties, reputational damage, increased audit requirements, loss of payment processing rights, and heightened breach risk.
4. How long does PCI DSS certification take?
Answer: Depending on system complexity and security maturity, compliance can take anywhere from several weeks to several months.
5. Is penetration testing mandatory under PCI DSS?
Answer: Yes. Penetration testing and vulnerability scanning are required to identify exploitable weaknesses in systems that handle cardholder data.
