
The Rise of IoT: Securing Smart Devices in Network Infrastructure
The Internet of Things (IoT) and Operational Technology (OT) have revolutionized industries by enabling seamless connectivity, automation, and smart infrastructure. From connected thermostats in smart homes to sensors in manufacturing plants, these devices have become integral to daily operations and modern lifestyles. However, their widespread adoption comes with a significant trade-off: security.
IoT and OT devices often operate within critical network infrastructures, making them prime targets for cyberattacks. Unlike traditional IT systems, these devices bring unique security challenges that demand specialized testing and mitigation strategies.
In this blog, we’ll explore The Rise of IoT: Securing Smart Devices in Network Infrastructure and security challenges posed by IoT and OT devices, common vulnerabilities, and advanced tools and techniques for securing them through Vulnerability Assessment and Penetration Testing (VAPT).
Security Challenges Unique to IoT and OT
IoT and OT devices differ fundamentally from traditional IT systems, creating unique challenges:
1. Heterogeneity of Devices
IoT ecosystems consist of a wide range of devices, from smart bulbs to industrial sensors, often developed by different manufacturers using proprietary operating systems and communication protocols. This diversity makes it difficult to apply standardized security practices or conduct uniform assessments. Each device may require a tailored testing approach.
2. Limited Resources
Many IoT devices are designed to perform specific tasks with minimal hardware, meaning they lack the processing power, memory, or battery life to support advanced security measures like encryption or endpoint protection. These constraints leave them vulnerable to attacks that would be thwarted in traditional systems.
3. Long Device Lifecycles
Operational Technology devices, such as those in industrial settings, are built for longevity, often running for decades. Unfortunately, their security measures may not keep up with evolving cyber threats, leaving legacy systems open to exploitation.
4. Lack of Security by Design
Manufacturers of IoT devices often prioritize cost and functionality over security. This oversight leads to vulnerabilities such as default credentials, unprotected firmware, and insecure communication protocols.
5. High Stakes in OT Environments
OT devices are critical to essential services like energy, healthcare, and transportation. Any compromise in these environments can lead to catastrophic consequences, including operational shutdowns, financial losses, or even risks to human life.
Common IoT Vulnerabilities
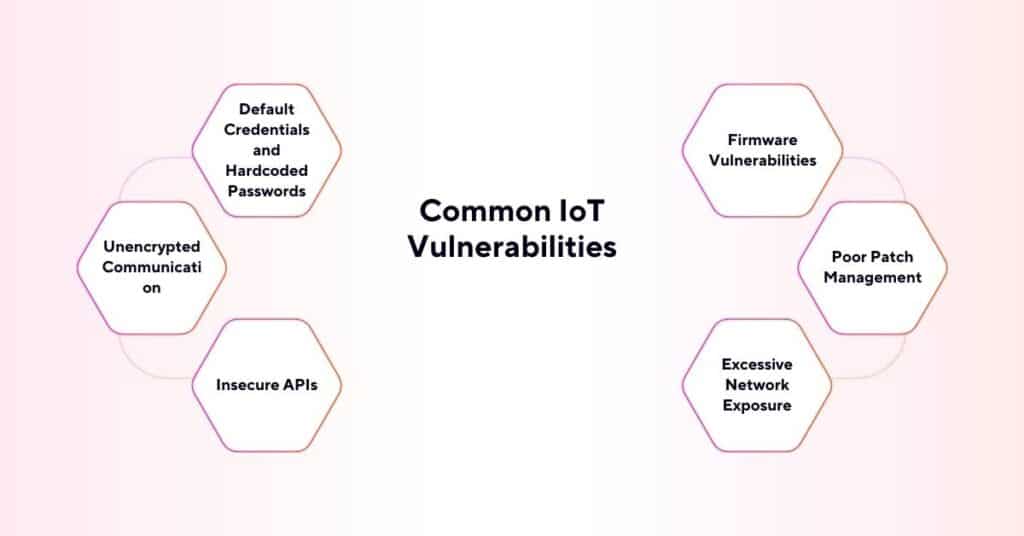
IoT devices are riddled with vulnerabilities that attackers exploit to compromise networks. Here are the most prevalent:
1. Default Credentials and Hardcoded Passwords
Many IoT devices are shipped with default usernames and passwords like “admin” and “12345,” which users often neglect to change. Attackers exploit this low-hanging fruit to gain unauthorized access. Hardcoded credentials, embedded directly in the device firmware, are even harder to mitigate.
2. Unencrypted Communication
Unsecured protocols, such as HTTP or plain-text communication, expose IoT devices to eavesdropping and interception. Attackers can exploit these vulnerabilities to intercept sensitive data or manipulate device behavior.
3. Insecure APIs
Application Programming Interfaces (APIs) are widely used to enable communication and integration between IoT devices and other systems. Poorly secured APIs, lacking proper authentication and input validation, can serve as a direct entry point for attackers.
4. Firmware Vulnerabilities
IoT device firmware often contains coding flaws, unpatched bugs, or outdated software. Attackers can reverse-engineer firmware to uncover vulnerabilities or inject malicious code.
5. Poor Patch Management
IoT devices frequently lack mechanisms for automatic updates, leaving them exposed to known vulnerabilities. In some cases, manufacturers cease support for devices after a few years, exacerbating the problem.
6. Excessive Network Exposure
Many IoT devices are connected directly to the internet, exposing them to threats. Tools like Shodan, a search engine for connected devices, allow attackers to locate exposed IoT endpoints easily.
Tools and Techniques for Testing IoT Devices in a Network Environment
Securing IoT devices requires a nuanced approach to VAPT. Below are tools and techniques tailored to the specific challenges of IoT security:
1. Environment Mapping
Mapping out the IoT and OT environment is the first step. Tools like Nmap and IoT Inspector can identify connected devices, their IP addresses, open ports, and operating systems. This inventory lays the groundwork for targeted testing.
2. Credential Testing
Automated tools like Hydra or Medusa can be used to test default credentials or brute-force passwords. Penetration testers can assess how easily an attacker might gain unauthorized access to devices.
3. Communication Analysis
Intercepting device communications using Wireshark or Burp Suite can reveal insecure transmissions, such as unencrypted data or weak protocols. Identifying these vulnerabilities is critical for ensuring secure data exchange.
4. Firmware Analysis
Firmware contains the operational code of IoT devices. Tools like Binwalk and Firmadyne allow testers to extract and analyze firmware for hardcoded passwords, insecure configurations, or exploitable code. Reverse engineering firmware helps uncover vulnerabilities invisible during standard network scans.
5. Vulnerability Scanning
IoT-specific vulnerability scanning tools like Nessus and OpenVAS identify known weaknesses in devices. These scans can pinpoint insecure configurations, outdated firmware, and exposure to common exploits.
6. Simulating Botnet Recruitment
IoT botnets, like Mirai, exploit default credentials and unprotected endpoints. Simulating botnet recruitment can help assess how well devices resist these attacks and inform countermeasures.
7. Testing Physical Security
IoT devices are often physically accessible. Penetration testers should assess vulnerabilities like USB ports with debug access, hardware interfaces like JTAG, or weak physical enclosures.
8. Emulating Malicious Updates
Test devices for their ability to validate firmware authenticity by emulating unauthorized updates. Devices should enforce cryptographic signing of firmware to prevent tampering.
Securing IoT and OT Networks
After identifying vulnerabilities, remediation should focus on these key areas:
1. Change Default Settings
Mandate the replacement of default credentials and disable unused features during device setup.
2. Enforce Encryption
Use secure communication protocols (e.g., HTTPS, TLS) to protect data in transit.
3. Regular Updates
Ensure devices are patched promptly to address vulnerabilities. For unsupported devices, consider replacing them.
4. Network Segmentation
Separate IoT devices from critical IT networks using VLANs, firewalls, or dedicated subnets.
5. Continuous Monitoring
Deploy IoT-specific intrusion detection systems (IDS) to monitor device behavior and detect anomalies.
Explore the Network Infrastructure VAPT Series
Are you curious about how to secure your network infrastructure effectively? You’re in the right place! This blog series is your ultimate guide to understanding and mastering Network Infrastructure Vulnerability Assessment and Penetration Testing (VAPT). Whether you’re just starting out or looking to level up your skills, we’ve got you covered.
Conclusion
The rapid integration of IoT and OT devices into critical infrastructure has reshaped the cybersecurity landscape. With their unique challenges and vulnerabilities, securing these devices is paramount to protecting both organizations and individuals.
Through specialized tools and advanced VAPT techniques, security professionals can uncover hidden flaws and recommend robust mitigation strategies. The journey to securing IoT devices isn’t just about addressing vulnerabilities—it’s about building trust in the connected systems that power our modern world.
