Top 10 Vulnerability Assessment and Penetration Testing Companies in Bengaluru
Vulnerability Assessment and Penetration Testing (VAPT) are essential cybersecurity practices that help organisations identify, evaluate, and validate security weaknesses across their IT infrastructure, applications, and networks. Vulnerability assessment focuses on systematically uncovering potential flaws, while penetration testing ethically simulates real-world attacks to determine how exploitable those weaknesses are and the potential business impact.
As India’s leading technology and innovation hub, Bengaluru has witnessed rapid growth in IT services, SaaS, fintech, cloud-native startups, and global R&D centres. With accelerated digital transformation, widespread cloud adoption, stricter compliance expectations, and a rise in targeted cyber threats, VAPT has become a necessity rather than a choice. Organisations across banking, IT services, healthcare, e-commerce, manufacturing, and startups must continuously assess their security posture to remain compliant, reduce risk, and ensure long-term cyber resilience.
- What is VAPT (Vulnerability Assessment and Penetration Testing)?
- Types of Vulnerability Assessment and Penetration Testing
- Why VAPT Is Important for Businesses in Bengaluru?
- How VAPT Helps Organisations Meet Compliance Standards
- 1. Identifying compliance gaps early
- 2. Validating security controls under real attack conditions
- 3. Providing audit-ready reports as documented evidence
- 4. Supporting risk-based remediation strategies
- 5. Aligning with ISO, SOC, PCI DSS, HIPAA, CERT-In, and NIST-based frameworks
- 6. Enabling continuous compliance as systems and environments evolve
- 7. Reducing the risk of breaches and non-compliance penalties
- Top 10 Vulnerability Assessment and Penetration Testing Companies in Bengaluru
- Proactive Cyber Defence Starts with VAPT
- FAQs
What is VAPT (Vulnerability Assessment and Penetration Testing)?
Vulnerability Assessment and Penetration Testing (VAPT) is a cybersecurity process used to identify, analyse, and validate security weaknesses within an organisation’s IT environment. This includes networks, systems, applications, APIs, and cloud infrastructure, providing a realistic view of how attackers could exploit vulnerabilities and what the real-world consequences might be.
What Does VAPT Include?
1. Vulnerability Assessment (VA)
Vulnerability assessment involves systematic scanning and analysis to identify known security issues such as misconfigurations, outdated software, weak credentials, missing patches, and insecure services. The objective is to create a prioritised list of potential security gaps before attackers can exploit them.
2. Penetration Testing (PT)
Penetration testing goes beyond identification by ethically simulating cyberattacks. Security professionals attempt to exploit identified vulnerabilities to assess severity, determine what data or systems could be compromised, and understand the real business impact of an attack.
Why Is VAPT Important?
- Identifies security weaknesses before attackers exploit them.
- Confirms real, exploitable risks rather than theoretical findings.
- Helps meet regulatory, client, and contractual security requirements.
- Strengthens the overall security posture.
- Reduces the likelihood of data breaches and financial loss.
Types of Vulnerability Assessment and Penetration Testing
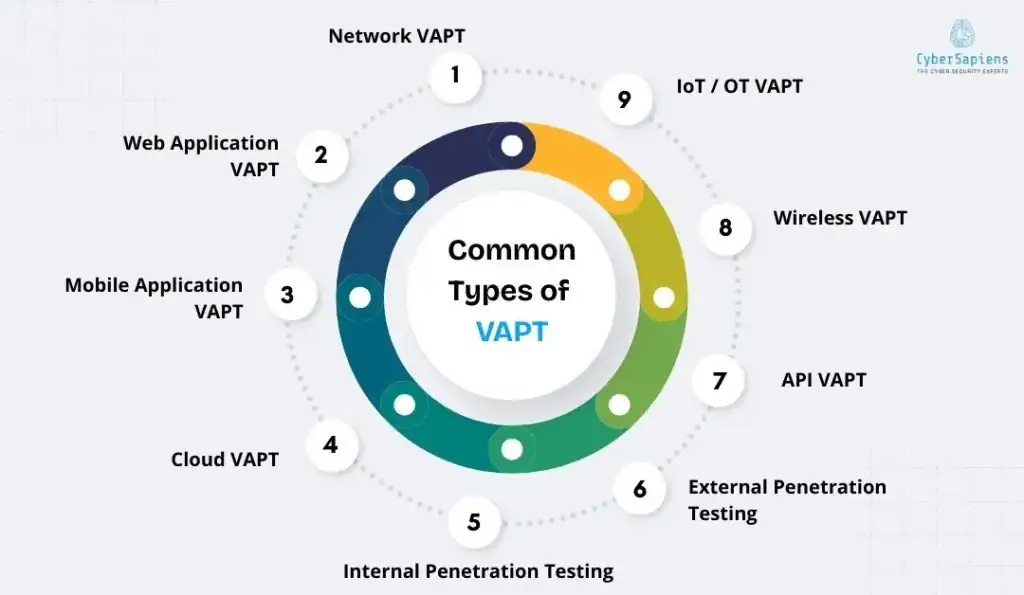
Different VAPT types focus on specific layers of an organisation’s IT environment. Together, they provide comprehensive visibility into security risks.
Common Types of VAPT
- Network VAPT: Assesses internal and external networks for open ports, insecure services, weak configurations, and network-level vulnerabilities.
- Web Application VAPT: Identifies OWASP Top 10 issues such as SQL injection, XSS, authentication flaws, broken access control, and insecure APIs.
- Mobile Application VAPT: Evaluates Android and iOS applications for insecure storage, weak encryption, API vulnerabilities, and mobile-specific threats.
- Cloud VAPT: Reviews AWS, Azure, and GCP environments for misconfigurations, excessive permissions, exposed storage, and IAM risks.
- Internal Penetration Testing: Simulates insider threats or compromised employee accounts.
- External Penetration Testing: Tests internet-facing systems from an external attacker’s perspective.
- API VAPT: Targets APIs for authorisation issues, data exposure, rate-limiting flaws, and logic vulnerabilities.
- Wireless VAPT: Assesses Wi-Fi networks for weak encryption, rogue access points, and unauthorised access.
- IoT / OT VAPT: Evaluates connected devices and operational systems for insecure firmware, default credentials, and protocol weaknesses.
Why VAPT Is Important for Businesses in Bengaluru?
Vulnerability Assessment and Penetration Testing play a critical role in securing organisations operating in Bengaluru’s highly competitive and innovation-driven ecosystem.
1. Expanding Cyber Threat Landscape
With large-scale cloud adoption, SaaS platforms, DevOps pipelines, and remote work environments, Bengaluru-based organisations face a constantly expanding attack surface. VAPT helps identify and remediate vulnerabilities before they are exploited.
2. Compliance and Client Security Expectations
Many organisations must comply with ISO 27001, SOC 2, PCI DSS, HIPAA, CERT-In guidelines, and client-mandated security audits. Regular VAPT demonstrates proactive risk management and audit readiness.
3. Cloud-First and SaaS-Driven Growth
As Bengaluru companies adopt cloud-native architectures, APIs, and microservices, VAPT ensures secure configurations and deployment practices across modern environments.
4. Protection of Sensitive Data
Industries such as fintech, healthcare, IT services, and global product companies handle sensitive customer and enterprise data. VAPT helps prevent data breaches, regulatory penalties, and reputational damage.
5. Business Continuity and Operational Resilience
By identifying exploitable weaknesses early, VAPT reduces the risk of ransomware attacks, service outages, and operational disruption.
6. Building Trust with Global Clients
VAPT reports provide documented proof of strong security practices, helping organisations build trust with international clients, partners, and auditors.
7. Cost-Effective Risk Management
Addressing vulnerabilities early through VAPT is significantly more cost-effective than dealing with incident response, legal exposure, and post-breach recovery.
How VAPT Helps Organisations Meet Compliance Standards
VAPT supports regulatory and industry compliance by:
1. Identifying compliance gaps early
Vulnerability Assessment and Penetration Testing help organisations detect security gaps, misconfigurations, and weak controls that could lead to non-compliance with regulatory or industry standards. Identifying these issues early allows teams to address them proactively, reducing audit findings, compliance delays, and last-minute remediation efforts.
2. Validating security controls under real attack conditions
Having security policies and controls in place is not enough if they fail during an actual attack. Penetration testing validates the effectiveness of implemented controls by simulating real-world attack scenarios, ensuring that access controls, network protections, application security mechanisms, and monitoring systems perform as intended.
3. Providing audit-ready reports as documented evidence
VAPT produces detailed, structured reports that document vulnerabilities, exploitation techniques, impact assessments, and remediation recommendations. These reports serve as reliable, audit-ready evidence for internal reviews, external audits, and regulatory assessments, demonstrating due diligence and compliance maturity.
4. Supporting risk-based remediation strategies
Modern compliance frameworks emphasise prioritising risks based on severity and business impact rather than a checklist approach. VAPT enables organisations to focus remediation efforts on the most critical and exploitable vulnerabilities, optimising security investments and reducing overall risk exposure.
5. Aligning with ISO, SOC, PCI DSS, HIPAA, CERT-In, and NIST-based frameworks
Many global and regional security standards explicitly recommend or require regular vulnerability assessments and penetration testing. VAPT supports compliance across multiple frameworks by fulfilling requirements related to risk assessment, security testing, and continuous monitoring.
6. Enabling continuous compliance as systems and environments evolve
IT environments constantly change due to cloud adoption, application updates, integrations, and infrastructure upgrades. Regular VAPT ensures these changes do not introduce new vulnerabilities or compliance gaps, helping organisations maintain continuous compliance rather than treating it as a one-time exercise.
7. Reducing the risk of breaches and non-compliance penalties
By proactively identifying and remediating exploitable vulnerabilities, VAPT significantly lowers the likelihood of security incidents that could result in data breaches, regulatory penalties, legal liabilities, and reputational damage.
Top 10 Vulnerability Assessment and Penetration Testing Companies in Bengaluru

1. CyberSapiens
CyberSapiens delivers end-to-end VAPT services across Bengaluru, combining automated vulnerability discovery with deep manual penetration testing. Their compliance-ready reporting maps findings to ISO 27001, SOC 2, PCI DSS, HIPAA, and CERT-In expectations.
CyberSapiens Vulnerability Assessment & Penetration Testing (VAPT) Services
1. Web Application VAPT
CyberSapiens performs comprehensive security assessments of web applications to uncover weaknesses that attackers could exploit. Testing covers OWASP Top 10 vulnerabilities such as SQL injection, cross-site scripting (XSS), authentication failures, access control gaps, and insecure session handling, ensuring applications are robust against real-world threats.
2. Mobile Application VAPT
This service evaluates the security of Android and iOS applications by identifying risks, including insecure data storage, weak encryption, unsafe API interactions, reverse-engineering exposure, and authentication flaws. Both static and dynamic analysis techniques are applied throughout the mobile app lifecycle.
3. Cloud VAPT
CyberSapiens assesses cloud environments across AWS, Azure, and Google Cloud to detect misconfigurations, exposed services, excessive permissions, insecure storage, and identity-related risks. The assessments follow cloud security best practices and shared responsibility models.
4. IoT Device VAPT
IoT security testing reviews connected devices, firmware, and communication protocols to identify issues such as weak authentication, insecure firmware updates, exposed interfaces, hardcoded credentials, and data interception risks, helping protect IoT ecosystems from physical and remote attacks.
5. Infrastructure VAPT
Infrastructure assessments cover servers, operating systems, databases, and internal systems. CyberSapiens identifies unpatched components, insecure configurations, privilege escalation paths, and exposed services across on-premise and hybrid environments.
6. API VAPT
API security testing focuses on backend services and integrations, uncovering broken authentication, excessive data exposure, inadequate rate limiting, injection vulnerabilities, and business logic abuse—critical for microservices architectures, mobile applications, and third-party integrations.
7. Network VAPT
Network testing evaluates internal and external networks for open ports, weak segmentation, insecure protocols, misconfigured firewalls, and lateral movement risks, reducing the chances of unauthorised access and internal compromise.
8. Thick Client and Thin Client VAPT
This service assesses desktop-based (thick client) and browser-based (thin client) applications for insecure communications, client-side logic flaws, weak authentication mechanisms, and reverse-engineering risks, ensuring secure interaction with backend systems.
2. SISA
SISA is a well-established cybersecurity firm known for its deep expertise in penetration testing, risk assessments, and regulatory-driven security testing. The company has strong experience in BFSI, fintech, and payment ecosystems, helping organisations identify exploitable vulnerabilities while meeting industry security and compliance expectations.
3. Wipro Cybersecurity
Wipro Cybersecurity provides enterprise-scale Vulnerability Assessment and Penetration Testing services across applications, networks, cloud platforms, and infrastructure. Their VAPT offerings are integrated into broader security and risk management programmes for global enterprises.
4. Infosys Cybersecurity
Infosys Cybersecurity delivers vulnerability assessments and penetration testing as part of large-scale enterprise security engagements. Their services support organisations in identifying security gaps across complex IT environments while aligning testing with business and compliance requirements.
5. Secureworks
Secureworks offers advanced penetration testing and threat-led security testing designed to simulate real-world attack scenarios. Their approach helps enterprises understand how attackers could compromise systems and prioritise remediation based on actual risk.
6. HackerOne
HackerOne supports penetration testing and coordinated vulnerability disclosure through ethical hacker programmes. Organisations leverage their global security researcher community to identify vulnerabilities across applications and infrastructure in a responsible and structured manner.
7. Factosecure
Factosecure provides risk-based VAPT services with a focus on identifying high-impact and exploitable vulnerabilities. Their assessments help organisations prioritise remediation efforts based on severity, exploitability, and potential business impact.
8. Mirox
Mirox offers Vulnerability Assessment and Penetration Testing along with security audit services to help organisations identify weaknesses across networks, applications, and infrastructure, supporting improved security posture and audit readiness.
9. DTS Solution
DTS Solution specialises in network, application, and infrastructure penetration testing, along with ongoing vulnerability management services. Their assessments help organisations uncover security gaps and reduce exposure to cyber threats.
10. Wattlecorp
Wattlecorp delivers comprehensive vulnerability assessments, penetration testing, and cloud security reviews for Indian enterprises. Their services cover internal and external testing, application security, and cloud risk identification.
Proactive Cyber Defence Starts with VAPT
Vulnerability Assessment and Penetration Testing are no longer optional for organisations operating in Bengaluru’s fast-paced digital ecosystem. Choosing the right VAPT partner helps businesses identify real risks, strengthen defences, and meet compliance and global client expectations with confidence. Investing in professional VAPT services is a critical step toward proactive risk management, long-term resilience, and trust.
FAQs
1. How often should organisations perform VAPT?
Answer: At least annually, and whenever significant changes occur, such as new applications, cloud migrations, infrastructure upgrades, or compliance requirements.
2. What systems can be tested under VAPT?
Answer: Web applications, mobile apps, APIs, cloud environments, networks, infrastructure, IoT devices, and internal systems.
3. Is VAPT mandatory for compliance?
Answer: Many standards, including ISO 27001, SOC 2, PCI DSS, HIPAA, and CERT-In guidelines, strongly recommend or mandate regular VAPT.
4. Is VAPT only for large enterprises?
Answer: No. Startups and mid-sized organisations also require VAPT, especially when handling sensitive data or operating cloud-based platforms.
5. Why choose a professional VAPT provider like CyberSapiens?
Answer: Professional providers deliver accurate testing, real-world attack simulation, actionable remediation, and compliance-ready reporting not just automated scan results.