Understanding Nmap Scans in Network Vulnerability Assessment and Penetration Testing (VAPT)
In Network Vulnerability Assessment and Penetration Testing (VAPT), Nmap is an indispensable tool. It offers deep insights into network configurations, services, and potential vulnerabilities.
For network security professionals and ethical hackers, mastering Nmap scans is crucial for identifying and mitigating risks.
This blog will explore key aspects of Nmap scans and how they play a pivotal role in VAPT.
5 Reasons why Nmap is one of the Best Tools for VAPT
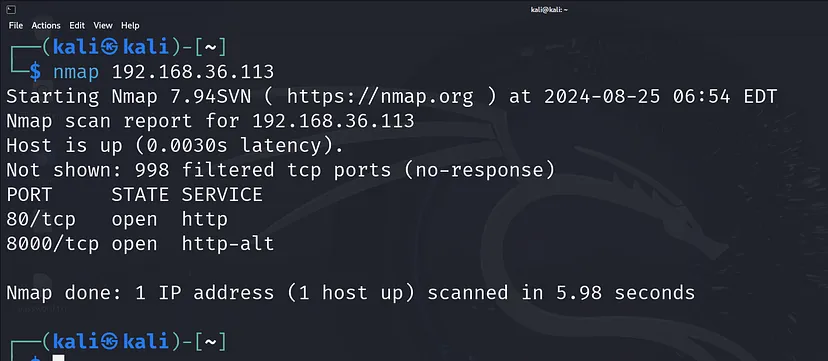
1. Open Ports and Services: The First Line of Defence
Why It’s Crucial in VAPT:
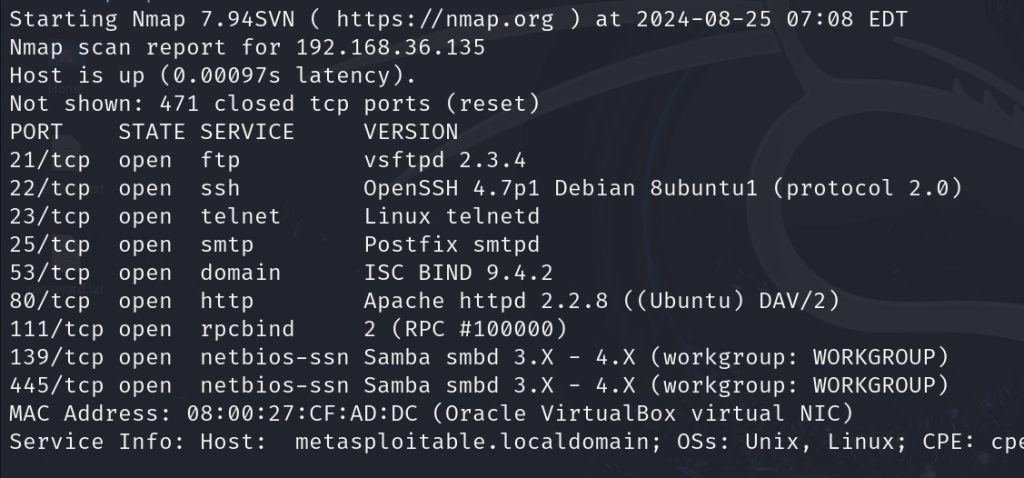
Open ports are gateways into a system. Each port typically corresponds to a service or application, and the state of these ports reveals how accessible a network is. Identifying which ports are open helps security professionals understand what services are exposed and potentially vulnerable.
What to Focus On:
- Port Number and State: Determine which ports are open, closed, or filtered. Open ports are critical because they represent active entry points that attackers might exploit.
- Service and Version Information: Knowing what service is running on a port (e.g., HTTP, SSH) and its version helps in assessing potential vulnerabilities associated with that service. For example, an outdated web server version might have known exploits.
Potential Risks:
Attackers can exploit open ports and outdated services. A port running an unpatched service might provide unauthorized access or expose sensitive data.
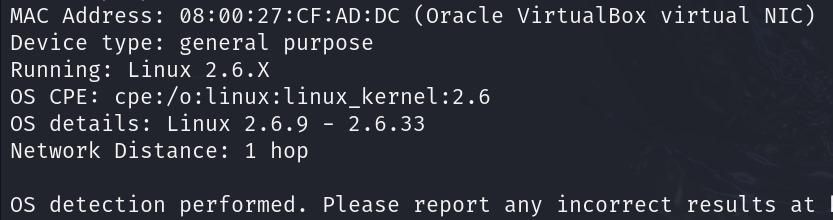
2. Operating System (OS) Detection: Tailoring Your Approach
Why It’s Crucial in VAPT:
Identifying the operating system of a target machine is essential for tailoring your penetration testing efforts. Different operating systems have different vulnerabilities, and knowing the OS helps you focus on relevant exploits and security measures.
What to Focus On:
- OS Fingerprinting: Use Nmap to detect the operating system running on the target. This includes identifying specific versions and types, which can be crucial for customizing your testing strategy.
- Accuracy and Verification: While Nmap’s OS detection is powerful, it might not always be accurate. Cross-verify results with other tools or techniques if needed.
Potential Risks:
An outdated or unsupported OS can have critical vulnerabilities. Attackers exploit these weaknesses if they are not patched or mitigated.
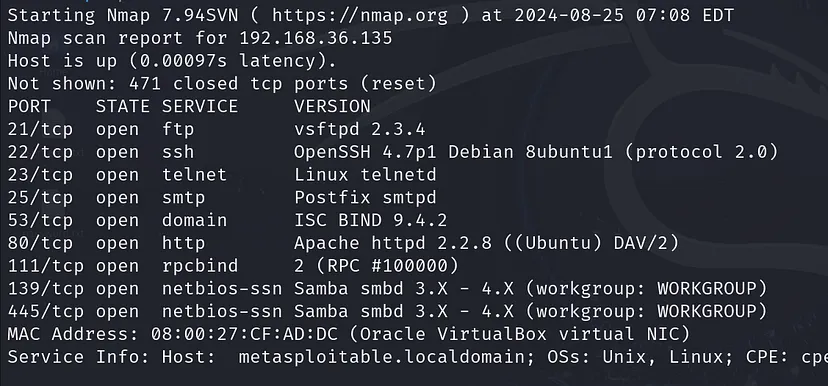
3. Version Detection: Uncovering Vulnerabilities
Why It’s Crucial in VAPT:
Version detection helps pinpoint specific software versions running on open ports, which can be critical in identifying vulnerabilities. Many exploits are version-specific, so knowing the exact version can help you understand which vulnerabilities might be present.
What to Focus On:
- Service Version Details: For each open port, Nmap attempts to identify the exact version of the service. This information is crucial for assessing whether the service is vulnerable to known exploits.
- Cross-Referencing with Vulnerability Databases: Once you have version details, check them against databases like CVE (Common Vulnerabilities and Exposures) to identify potential issues.
Potential Risks:
Outdated software versions can have known vulnerabilities that are easily exploitable. Keeping software updated and patched is essential for reducing risk.
4. Nmap Scripting Engine (NSE): Advanced Vulnerability Scanning
Why It’s Crucial in VAPT?
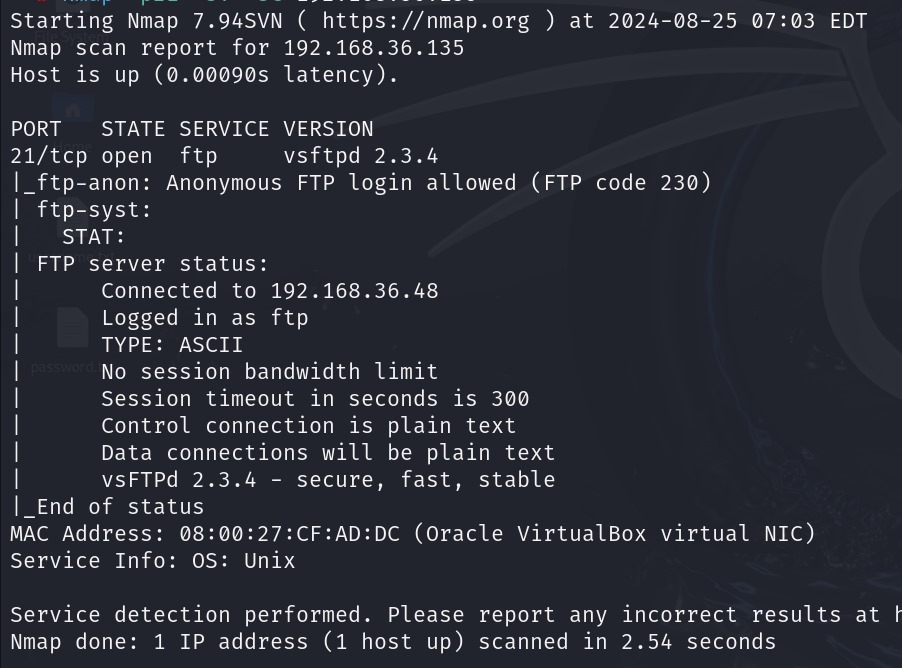
Nmap’s Scripting Engine (NSE) allows for advanced scanning capabilities by running custom scripts to detect vulnerabilities, enumerate services, and more. NSE scripts can uncover security issues that might not be visible through basic scans.
What to Focus On?
- Vulnerability Detection Scripts: Use NSE to run scripts that check for specific vulnerabilities (e.g., Heartbleed, SMB weaknesses). These scripts can provide in-depth analysis beyond simple port scanning.
- Service and Configuration Checks: NSE can reveal detailed information about services, such as SSL/TLS configurations and exposed resources. It can also identify potential misconfigurations or security weaknesses.
Potential Risks:
NSE scripts can detect critical vulnerabilities that might be overlooked in standard scans. Addressing these vulnerabilities is crucial for strengthening network security.
5. Other Key Considerations: Comprehensive Assessment
Firewall and IDS/IPS Detection:
- Firewall Impact: Ports reported as filtered often indicate a firewall is in place, which can affect scan results. Understanding how firewalls and IDS/IPS systems interact with your scans is essential for accurate vulnerability assessment.
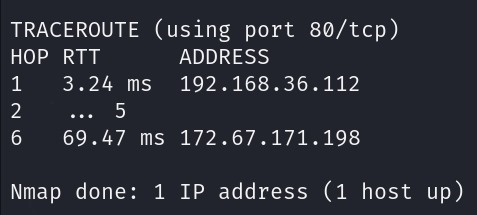
Traceroute and Network Topology Mapping:
- Network Path Analysis: Using traceroute features in Nmap helps map the network path between your scanning system and the target. This can reveal network architecture, identify potential chokepoints, and aid in planning effective penetration tests.
Service Misconfigurations:
- Unsecured Services: Misconfigurations, such as databases exposed to the internet without proper authentication, can pose significant risks. NSE can help identify such issues, which are critical for maintaining a secure network environment.
Special thanks
Dheeraj Prabhu K, Senior Security Analyst at CyberSapiens, for contributing his expertise to this content.
Conclusion
Nmap is a powerful tool in the Network Vulnerability Assessment and Penetration Testing (VAPT) arsenal.
By focusing on open ports, services, OS and version detection, and advanced NSE scripting, you can gain a comprehensive understanding of a network’s security posture. This information is vital for identifying vulnerabilities, assessing risks, and implementing effective security measures.
Understanding and utilizing Nmap’s capabilities effectively will enhance your ability to conduct thorough and impactful security assessments.
