
Best Phishing Simulation Platform for Universities and Colleges in Australia
Universities and colleges across Australia are facing an unprecedented rise in cyber threats. Over the last year, Australian educational institutions have become frequent victims of advanced phishing attacks ranging from fake fee reminders to fraudulent internship offers, fake scholarship approvals, and cloned university login portals. Because universities issue official campus email IDs to every student and faculty member, attackers are exploiting this trust to reach thousands of inboxes instantly.
This growing threat landscape has made one question critical: What is the Best Phishing Simulation Platform for Universities and Colleges in Australia? Students are often inexperienced in cybersecurity, while faculty and administrators juggle academic responsibilities, research, and administrative tasks. This combination creates the perfect environment for cybercriminals launching university and college-focused phishing scams that spread quickly and silently.
Most cybersecurity tools in the market focus purely on corporate users and overlook the dynamic, complex environment of educational institutions. Few offer simulation and awareness programs tailored for the academic sector. This creates a massive opportunity for universities and colleges to adopt a platform that strengthens student safety, protects faculty, and reduces institutional vulnerabilities.
PhishCare fills this gap by offering the Best Phishing Simulation Platform for Universities and Colleges in Australia, designed specifically for the academic environment and the unique threats faced by students and staff.
- Why Hackers Target Universities and Colleges?
- Types of Phishing Attacks Targeting Students and Staff
- Why Traditional Cyber Awareness Efforts Don’t Work in Australian Campuses?
- How PhishCare Awareness Training Protects Universities and Colleges in Australia?
- Why Cybersecurity Awareness Must Be a Priority in Australian Universities?
- How PhishCare Training Strengthens Campus Security?
- Empowering Students and Staff Through Cyber Awareness
- FAQs
- 1. Why is phishing simulation important for Australian universities?
- 2. Why is PhishCare the Best Phishing Simulation Platform for Universities and Colleges in Australia?
- 3. Can PhishCare help faculty who are not tech-savvy?
- 4. How often should universities run phishing simulations?
- 5. Is PhishCare suitable for large Australian universities?
Why Hackers Target Universities and Colleges?
You may assume your university account holds nothing of interest to cybercriminals, but it actually provides access to highly valuable resources. Here’s what makes your account a prime target:
- Library resources. Your account grants entry to paid academic journals and licensed digital materials, which criminals can illegally resell.
- Official university email. Emails sent from educational domains (especially those ending in .edu) are widely trusted. A compromised account allows attackers to send convincing spam or phishing messages.
- Your personal data. Through university portals, you can view and update sensitive details such as your address, financial information, emergency contacts, tax records, and direct deposit details, all attractive to scammers.
- Financial opportunities. Cybercriminals often impersonate university departments to request wire transfers or gift card payments. Any unexpected request for money should be treated with caution.
- Cloud storage and software access. Your account connects you to tools like Google Drive, Dropbox, and specialized academic software, all of which can be misused.
- Privileged or role-based access. Certain users, such as managers, researchers, or system administrators, hold elevated permissions and confidential information that attackers highly value.
- Network access. Your credentials allow entry into on-campus networks and VPN services, unlocking internal systems that are otherwise restricted.
Cybercriminals copy the email formats and send fake versions that look identical to legitimate communication. This is where the PhishCare becomes essential. When students experience simulations that replicate real Australian university phishing scams, they learn to pause, verify, and identify red flags before responding.
Types of Phishing Attacks Targeting Students and Staff
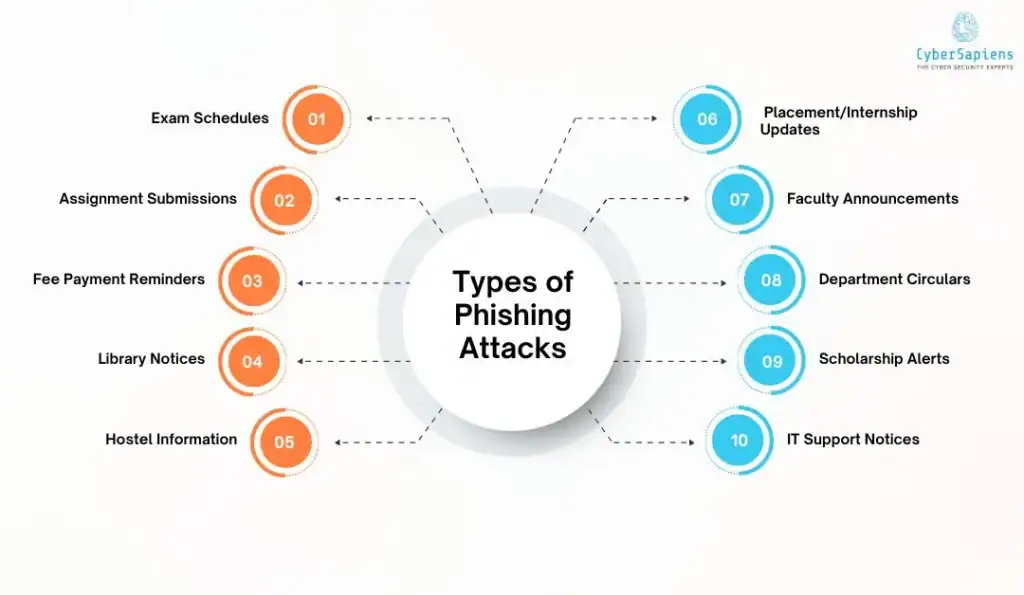
Phishing attacks in universities are becoming increasingly sophisticated, often disguised as everyday academic or administrative communications. Students and staff regularly receive emails about exams, assignments, fees, and campus updates, making it easy for attackers to blend malicious messages into the normal flow of university life. Below are some of the most common phishing tactics that specifically target the higher-education community.
1. Exam Schedules
Attackers send fake emails claiming to share updated or urgent exam schedules. Students may click on malicious links, thinking they are checking exam dates, making this a common and effective trick during peak academic periods.
2. Assignment Submissions
Cybercriminals impersonate professors or LMS platforms, sending fake submission links for assignments. When students upload files or log in, attackers steal their credentials or deliver malware.
3. Fee Payment Reminders
Students, especially international students, often receive legitimate fee reminders. Scammers exploit this by sending fraudulent notices urging immediate payment or sharing harmful “payment portals” that steal bank or card details.
4. Library Notices
Emails posing as the university library may warn about overdue books, expiring access, or new digital resources. These messages often contain links to credential-harvesting sites disguised as library login pages.
5. Hostel Information
Fake messages about hostel room allotments, maintenance alerts, or fee updates lure students into clicking malicious links. Attackers target first-year and outstation students who rely heavily on hostel communications.
6. Placement/Internship Updates
Students eager for job or internship opportunities are prime targets. Attackers send fake placement drives, interview calls, or internship offers that redirect to fraudulent forms designed to steal personal information.
7. Faculty Announcements
Scammers impersonate professors or department heads to send urgent academic updates, meeting requests, or material-sharing links. Because the emails appear authoritative, users are more likely to respond or click.
8. Department Circulars
Attackers mimic official circulars related to rules, events, policy changes, or departmental notices. These emails often include attachments that appear harmless but may contain malware.
9. Scholarship Alerts
Fake scholarship offers and renewal notices are increasingly common. Students are tricked into submitting sensitive documents or paying “processing fees” through fraudulent links.
10. IT Support Notices
Phishers frequently impersonate university IT teams with claims about mailbox storage issues, password expirations, or system upgrades. Users are directed to fake login portals that capture their credentials.
Why Traditional Cyber Awareness Efforts Don’t Work in Australian Campuses?
Many universities and colleges across Australia still depend on outdated cybersecurity awareness tactics, including:
- Posters and noticeboard messages
- Annual cybersecurity presentations
- Occasional email reminders
- Generic training videos that students tend to skip
These approaches lack practical, hands-on learning. Because they don’t replicate the pressure or realism of a real phishing attack, students and faculty quickly forget the information, leaving them vulnerable when an actual scam lands in their inbox.
How PhishCare Awareness Training Protects Universities and Colleges in Australia?
PhishCare combines real-world phishing simulation with instant Cyber Security Awareness Training to dramatically reduce risk. It teaches students, staff, and administrators how to recognize scams, how to report them, and how to verify legitimacy before taking action.
Below are the core reasons it works.
1. Realistic and Contextual Phishing Simulations for Australian Universities
PhishCare sends highly accurate simulations that mirror the most common university phishing scams seen across Australia today.
Examples of Australia-Specific Campus Phishing Attacks:
- Fake fee payment reminders imitating university finance departments
- Scholarship approval scams requesting bank details
- Phishing emails impersonating Student Services or Campus Administration
- Fake internship or placement offers pretending to be from Career Services
- Cloned university portal login pages for LMS systems
- Emails pretending to be from professors, HODs, or the Dean
- Password reset scams targeting university accounts
- Fraudulent library login pages
These scenarios are crafted to ensure simulations match real threats faced by Australian institutions. Because students and faculty interact with these realistic simulations in a safe environment, they develop long-term habits for identifying suspicious emails.
2. Instant Cyber Security Awareness Training for Maximum Impact
PhishCare delivers immediate “teachable moments.” When a student or faculty member clicks a simulated phishing email, they are redirected to a short, visual training lesson explaining:
- Why was the email suspicious?
- What red flags did they miss?
- How to avoid similar attacks in the future?
This instant feedback makes learning far more memorable compared to long workshops.
3. Detailed Reporting to Identify High-Risk Students and Departments
Visibility is essential for Australian universities, and PhishCare delivers detailed analytics that clearly show how users interact with phishing simulations. Administrators can see who clicked on a phishing email, who reported it, and who went as far as submitting their credentials. The platform also highlights which departments face higher risk, which students need additional training, and how performance improves across multiple campaigns. It even identifies repeat offenders and reveals the types of phishing attacks users struggle with the most. These insights allow university leaders to design targeted, data-driven interventions rather than relying on broad, generic training approaches.
4. Scalable for Small Colleges and Large Universities Across Australia
PhishCare is designed to scale seamlessly, making it suitable for both small colleges and large universities across Australia. Whether an institution serves 500 students or 60,000, the platform adapts effortlessly to growing user needs. It supports a wide range of educational environments, including public universities, private colleges, TAFEs, vocational training institutes, technical campuses, online education providers, and multi-campus institutions. This level of flexibility is a key reason PhishCare is recognized as the Best Phishing Simulation Platform for Universities and Colleges in Australia.
Why Cybersecurity Awareness Must Be a Priority in Australian Universities?
Australian universities operate in a highly connected, high-risk digital environment where thousands of students, staff, and researchers rely on email and online systems every day. This openness, combined with valuable research data and constant student turnover, makes academic institutions prime targets for cybercriminals. Strengthening cybersecurity awareness is no longer optional; it’s essential to protect campuses from email scams, data breaches, and financial fraud.
- Students are easy targets for attackers: Many students have limited cybersecurity awareness and are more likely to click on suspicious links or respond to deceptive messages.
- Phishing campaigns spread rapidly via email lists: A single malicious email can reach thousands of inboxes instantly through university-wide mailing systems, accelerating the impact of an attack.
- Attackers impersonate official university departments: Cybercriminals often mimic finance offices, student services, or IT support, making fraudulent emails appear highly credible.
- Fake fee scams are rising across Australia: Scammers increasingly send urgent, realistic messages demanding tuition, accommodation, or exam-related payments, tricking students into transferring money.
- Students rarely receive formal cybersecurity training: Most universities do not provide structured cyber awareness programs, leaving students unprepared to detect sophisticated phishing attacks.
- Financial and reputational damages can be severe: Successful attacks can lead to monetary losses for students and staff, while institutions face reputational harm, reduced trust, and costly remediation efforts.
How PhishCare Training Strengthens Campus Security?
PhishCare provides Australian educational institutions with:
- Real-world awareness without real-world consequences
- Behavioural change instead of theoretical knowledge
- Lower student vulnerability to phishing scam emails
- Better faculty recognition of suspicious LMS alerts
- Compliance-ready cybersecurity reports
- Protection of institutional reputation
This makes PhishCare the clear choice for the Best Phishing Simulation Platform for Universities and Colleges in Australia.
Empowering Students and Staff Through Cyber Awareness
Australian universities will continue to be targeted because of their structure, openness, and high student volume. While no tool can fully stop scam emails from arriving, training can stop people from falling for them.
This is exactly the mission of PhishCare. By combining highly realistic simulations with timely awareness lessons, PhishCare helps Australian institutions build cyber-aware students, faculty, and staff. This reduces risk at the human level, the most exploited weakness in academia.
FAQs
1. Why is phishing simulation important for Australian universities?
Answer: Because students and faculty receive frequent academic emails, attackers create fake versions to steal credentials. Simulations build practical awareness.
2. Why is PhishCare the Best Phishing Simulation Platform for Universities and Colleges in Australia?
Answer: It delivers realistic simulations tailored to Australian universities, paired with instant Cyber Security Awareness Training for maximum learning impact.
3. Can PhishCare help faculty who are not tech-savvy?
Answer: Yes. PhishCare is intuitive and designed for users with zero technical knowledge.
4. How often should universities run phishing simulations?
Answer: Monthly or quarterly campaigns are ideal for building consistent awareness.
5. Is PhishCare suitable for large Australian universities?
Answer: Absolutely. PhishCare is fully scalable for institutions with tens of thousands of users.
