
Best Phishing Simulation Platform for Universities and Colleges in New Zealand
Universities and colleges across New Zealand are facing a rapidly growing wave of cyber threats. Over the past year, New Zealand educational institutions have experienced a surge in sophisticated phishing attacks—from fake tuition fee reminders and fraudulent internship offers to cloned university login portals and deceptive scholarship approvals.
Because universities issue official campus email accounts to every student, staff member, and researcher, cybercriminals take advantage of this trust to reach thousands of inboxes instantly. This escalating threat landscape has made one question more critical than ever: What is the Best Phishing Simulation Platform for Universities and Colleges in New Zealand?
Students often have limited cybersecurity awareness, while lecturers, researchers, and administrators juggle academic responsibilities, research commitments, and administrative tasks. This creates the perfect environment for cybercriminals to launch highly targeted scams that spread quickly and silently across New Zealand campuses.
Most cybersecurity tools in the market are built for corporate environments and fail to address the dynamic, decentralised, and student-heavy nature of New Zealand’s academic system. Very few provide simulations tailored specifically to academic communication patterns.
This gap has opened a significant opportunity for New Zealand institutions to adopt a platform that strengthens student safety, protects faculty, and reduces overall cyber risk. PhishCare fills this gap by offering the Best Phishing Simulation Platform for Universities and Colleges in New Zealand, purpose-built for the academic environment and the unique threats faced by students and staff.
- Why Hackers Target Universities and Colleges in New Zealand?
- Types of Phishing Attacks Targeting Students and Staff in New Zealand
- Why Traditional Cyber Awareness Efforts Don’t Work in NZ Campuses?
- How PhishCare Protects Universities and Colleges in New Zealand?
- Why Cybersecurity Awareness Must Be a Priority in New Zealand Universities?
- How PhishCare Strengthens Campus Security in New Zealand?
- Empowering Students and Staff Through Cyber Awareness
- FAQs
- 1. Why is phishing simulation important for New Zealand universities?
- 2. Why is PhishCare the Best Phishing Simulation Platform for NZ institutions?
- 3. Is PhishCare suitable for non-technical staff?
- 4. How often should NZ institutions run simulations?
- 5. Can PhishCare support large NZ universities with multiple campuses?
Why Hackers Target Universities and Colleges in New Zealand?
A university account may seem harmless, but to cybercriminals, it offers access to high-value systems and sensitive information. Here’s why NZ student and staff accounts are prime targets:
1. Access to Academic & Research Resources
University accounts provide access to premium journals, specialised research tools, scholarly databases, and copyrighted academic materials. Because these resources are expensive and subscription-based, attackers who steal university credentials can illegally download and resell them on underground markets. This makes academic accounts a high-value target for cybercriminals.
2. Trusted .ac.nz and Educational Domains
Emails sent from .ac.nz addresses carry strong credibility within New Zealand’s academic community. Because recipients naturally trust communication from official university domains, these messages are opened and acted upon quickly. When attackers compromise even a single .ac.nz account, they can exploit that trust to distribute highly convincing phishing emails across entire faculties, student cohorts, and institutional mailing lists, dramatically increasing the reach and impact of the attack.
3. Sensitive Personal & Financial Information
University portals store personal data such as:
- Mailing addresses
- Fee payment details
- Emergency contacts
- Payroll/bank details for staff
- Student loan or scholarship data
These are highly valuable to scammers.
4. Financial Fraud Opportunities
Cybercriminals often pose as official university departments to trick students and staff into making payments. They send emails requesting refunds, urgent tuition balances, or administrative fees, directing recipients to fake payment portals that look legitimate. Once users enter their details, attackers steal the money and any sensitive information submitted.
5. Cloud Storage & LMS Access
Compromised university accounts can expose access to essential platforms like Microsoft 365, Google Workspace. With these credentials, attackers can view or steal research files, manipulate coursework, and access shared departmental drives. This level of access puts academic integrity, sensitive data, and institutional systems at significant risk.
6. Privileged Access & Research Data
Staff and researchers often have access to confidential projects, valuable intellectual property, and internal university systems. These high-value assets make them prime targets for attackers, who can exploit compromised accounts to steal sensitive information, interfere with ongoing research, or gain deeper access to institutional networks.
7. Campus Network Access
University credentials provide access to on-campus networks, VPN services, and restricted internal systems that aren’t available to the public. If attackers obtain these logins, they can move deeper into the university’s infrastructure, access protected resources, and exploit systems that are otherwise shielded from external threats.
Cybercriminals often copy the exact format of official university communication, making their emails almost indistinguishable from legitimate ones. This is where PhishCare becomes essential, teaching students and staff to pause and recognise red flags.
Types of Phishing Attacks Targeting Students and Staff in New Zealand
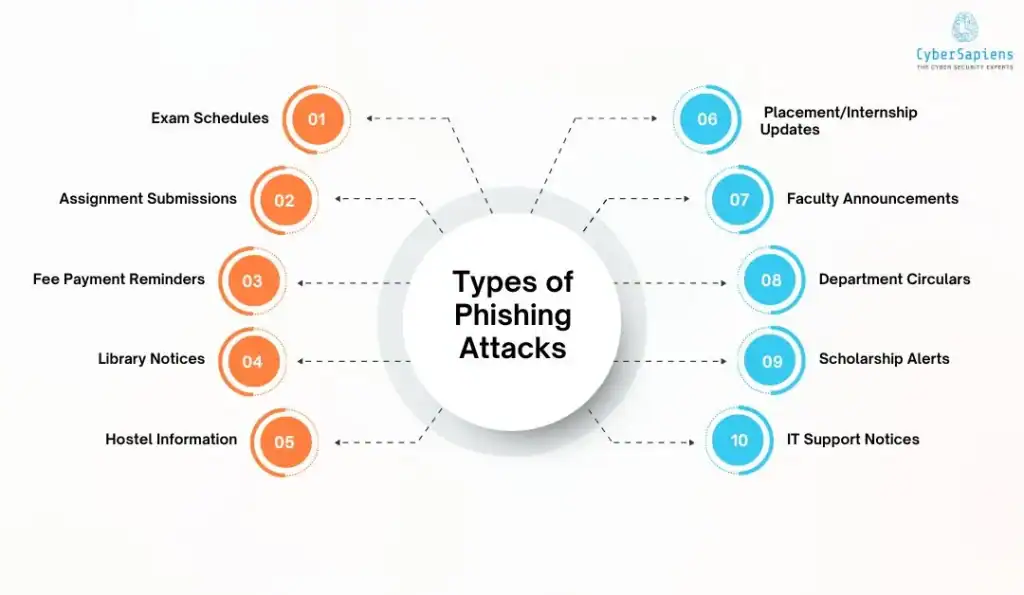
Phishing attacks in NZ’s higher education sector are becoming increasingly refined and often mimic everyday campus communication. Students and staff routinely receive messages about exams, assignments, fees, and academic updates, making it easy for attackers to blend in.
Below are the most common phishing tactics targeting NZ universities and colleges:
1. Exam Schedules
Scammers send emails claiming to provide updated or urgent exam schedules, resits, or timetable changes. These messages appear to come from the Exams Office or academic departments. When students click the attached link, they are redirected to fake university login pages designed to steal credentials, especially during exam seasons.
2. Assignment Submissions
Cybercriminals impersonate lecturers, teaching assistants, or LMS platforms like Moodle or Canvas. They send messages saying that an assignment is due, overdue, or requires resubmission. Clicking the link leads students to malicious upload portals or cloned LMS login pages that harvest passwords.
3. Fee Payment Reminders
Fake tuition or course-related fee reminders are common, especially for international students. These emails use urgent language (“Immediate Payment Required,” “Final Warning”) and link to fraudulent payment portals where attackers steal bank details or credit card information.
4. Library Notices
Attackers mimic the university library system, sending emails about expiring book loans, overdue items, or access to new e-resources. The links redirect students and staff to fake “library login” pages where university credentials are captured.
5. Hostel Information
Residence hall students regularly receive notices about maintenance, room allocations, safety updates, or billing changes. Attackers take advantage by sending fake messages about room changes or urgent housing payments. First-year students and international students are especially vulnerable.
6. Placement & Internship Offers
Cybercriminals impersonate Careers Services or well-known companies, offering internships, apprenticeships, or part-time job opportunities. These emails lead to fake application forms that collect personal data such as full names, phone numbers, addresses, and academic details sometimes even NZ bank account information.
7. Faculty Announcements
These phishing messages appear to come from lecturers, programme leaders, or heads of department. They may include “updated lecture slides,” “urgent instructions,” or “class cancellations.” Because they appear authoritative, recipients often click without verifying.
8. Department Circulars
Attackers create emails that look like official departmental circulars about policy updates, academic rules, timetables, lab sessions, workshops, or events. The attachments or links usually contain malware or credential-stealing forms.
9. Scholarship Alerts
Fake scholarship award, renewal, or eligibility emails are a growing threat. Students are asked to provide sensitive information, upload identity documents, or pay processing fees. These scams are especially effective during the start of new academic terms or fee payment cycles.
10. IT Support Notices
One of the most dangerous phishing types involves impersonating the university IT Helpdesk. These emails warn about mailbox storage limits, account suspension, password expiry, or multi-factor authentication updates. The links lead to perfectly mimicked login pages that capture .ac.nz credentials.
Why Traditional Cyber Awareness Efforts Don’t Work in NZ Campuses?
New Zealand campuses are dealing with increasingly sophisticated phishing and email-based scams, yet many institutions still rely on outdated awareness programs that no longer reflect modern threat tactics. Traditional cyber training often lacks relevance, realism, and engagement leaving students and staff unprepared for real attacks.
Many New Zealand institutions still rely on outdated cyber awareness efforts, such as:
- Posters and noticeboard warnings
- Annual cybersecurity seminars
- Occasional email reminders
- Generic online training modules
These approaches lack real-world impact. They do not simulate the urgency or realism of actual phishing attempts, which makes students and staff forget the training when a real threat appears.
How PhishCare Protects Universities and Colleges in New Zealand?
PhishCare combines realistic phishing simulations with immediate, contextual awareness training to dramatically lower the likelihood of successful attacks. Here’s why it works so effectively:
1. Realistic & Contextual Phishing Simulations for New Zealand Universities
PhishCare sends high-quality simulations that mirror the most common phishing scams affecting NZ campuses today.
Examples of New Zealand–Specific Phishing Attempts:
- Fake fee payment reminders mimicking Student Finance
- Scholarship approval scams requesting bank details
- Emails impersonating Student Services or Admissions
- Fake internship or placement offers from the Careers Services
- Cloned Moodle or university portal login pages
- Emails pretending to be from lecturers, programme leaders, or deans
- Password reset scams targeting .ac.nz accounts
- Fraudulent library access messages
These simulations match real threats students and staff encounter, making training more relevant and memorable.
2. Instant Cyber Security Awareness Training for Maximum Impact
When a user interacts with a simulated phishing message, PhishCare redirects them to a brief, visual lesson that explains:
- Why was the email suspicious
- What red flags did they miss
- How to detect similar scams in the future
This “learn-in-the-moment” approach promotes long-term behavioural change far better than traditional workshops.
3. Detailed Reporting to Identify High-Risk Users & Departments
Visibility is critical for New Zealand tertiary institutions.
PhishCare provides detailed analytics showing:
- Who clicked
- Who reported
- Who submitted credentials
- Which departments or faculties are high-risk
- Repeat offenders
- Skills gaps in identifying certain phishing types
- Performance improvements across campaigns
This helps cybersecurity teams deliver targeted, data-backed interventions.
4. Scalable for Small Colleges and Large NZ Universities
PhishCare is built to support all types of New Zealand education providers, including:
- Public universities
- Polytechnics and Institutes of Technology
- Private training establishments (PTEs)
- Wānanga
- Vocational education providers
- Multi-campus institutions
- Online and hybrid learning platforms
Whether serving 500 learners or 40,000 students, PhishCare scales seamlessly.
Why Cybersecurity Awareness Must Be a Priority in New Zealand Universities?
Cyber threats targeting New Zealand universities are becoming more advanced, putting research data, financial information, and student records at risk. With campuses increasingly dependent on digital platforms, even a single phishing email can lead to major disruptions. This makes cybersecurity awareness not just important, but a critical priority for every New Zealand university.
NZ tertiary institutions face constant cyber threats because:
- Students are easy targets with low awareness
- Phishing spreads instantly through academic mailing lists
- Attackers impersonate official university departments
- Tuition-related scams are rising
- Few academic programmes include cyber awareness training
- Successful attacks cause financial loss and reputational damage
How PhishCare Strengthens Campus Security in New Zealand?
New Zealand universities need stronger, more practical defences to keep up with modern phishing and email-based attacks. PhishCare provides realistic simulations, behaviour-focused training, and actionable insights that help students and staff detect threats before they cause harm.
PhishCare provides New Zealand educational institutions with:
- Real-world awareness without real-world consequences
- Behavioural improvement instead of passive learning
- Lower student vulnerability to phishing scams
- Better staff recognition of suspicious emails
- Compliance-ready cybersecurity reporting
- Enhanced protection of institutional reputation
This makes PhishCare the leading choice for the Best Phishing Simulation Platform for Universities and Colleges in New Zealand.
Empowering Students and Staff Through Cyber Awareness
New Zealand universities and colleges will continue to be targeted due to their openness, diverse student base, and widespread use of digital systems. While no platform can prevent phishing emails from arriving, training can prevent people from falling for them.
This is the core mission of PhishCare. By combining realistic simulations with instant cyber awareness lessons, PhishCare helps NZ institutions build cyber-aware students, staff, and faculty, reducing risk at the human level, the most exploited weakness in higher education.
FAQs
1. Why is phishing simulation important for New Zealand universities?
Answer: Because attackers frequently impersonate university departments, realistic simulations prepare students and staff to identify these scams.
2. Why is PhishCare the Best Phishing Simulation Platform for NZ institutions?
Answer: It delivers NZ-specific simulations paired with instant training, making learning practical and memorable.
3. Is PhishCare suitable for non-technical staff?
Answer: Yes. It’s extremely user-friendly and designed for users with zero technical background.
4. How often should NZ institutions run simulations?
Answer: Monthly or quarterly campaigns are ideal for consistent improvement.
5. Can PhishCare support large NZ universities with multiple campuses?
Answer: Absolutely. PhishCare was built to scale effortlessly across large and multi-campus environments.
