
Top 10 Different Types of Cyber Security Services
Cyber Security has become a top priority for individuals, businesses, and governments alike. With the increasing number of cyber threats and attacks, it’s essential to have a robust cybersecurity system in place to protect sensitive information and prevent financial losses.
Cyber Security services have become a vital component of any organization’s IT infrastructure, and there are various types of services available to cater to different needs. In this article, we’ll explore the top 10 different types of cybersecurity services that can help protect your digital assets.
- List of Top 10 Different Types of Cyber Security Services
- How to Choose the Right Cybersecurity Service?
- Summary: Top 10 Different Types of Cyber Security Services
- Conclusion:
- FAQs: Top 10 Different Types of Cyber Security Services
- 1. What is the primary goal of cybersecurity services?
- 2. What types of organizations need cybersecurity services?
- 3. What is the difference between penetration testing and vulnerability assessment?
- 4. How often should an organization conduct a cybersecurity risk assessment?
- 5. What is the role of incident response in cybersecurity services?
- 6. Can cybersecurity services be outsourced?
- 7. is the importance of security awareness training in cybersecurity services?
- 8. How can an organization measure the effectiveness of its cybersecurity services?
- 9. What is the role of cloud security in cybersecurity services?
- 10. How can an organization choose the right cybersecurity service provider?
List of Top 10 Different Types of Cyber Security Services

1. Penetration Testing
Penetration testing, also known as pen testing, is a type of cybersecurity service that involves simulating a real-world attack on a computer system, network, or web application to test its defences.
The goal of pen testing is to identify vulnerabilities and weaknesses that an attacker could exploit, and to provide recommendations for remediation. Penetration testers use various tools and techniques to attempt to breach the system, and their findings are used to strengthen the organization’s security posture.
2. Incident Response
Incident response is a type of cybersecurity service that involves responding to and managing security incidents, such as data breaches, malware outbreaks, or denial-of-service (DoS) attacks. Incident response services help organizations to quickly respond to security incidents, contain the damage, and restore normal operations.
This type of service typically includes incident detection, containment, eradication, recovery, and post-incident activities.
3. Vulnerability Assessment
Vulnerability assessment is a type of cybersecurity service that involves identifying and prioritizing vulnerabilities in an organization’s systems, networks, and applications.
This service helps organizations understand their security posture and take corrective action to remediate vulnerabilities before they can be exploited by attackers. Vulnerability assessment services typically include network scanning, configuration analysis, and vulnerability reporting.
4. Security Information and Event Management (SIEM)
Security Information and Event Management (SIEM) is a type of cybersecurity service that involves monitoring and analyzing security-related data from various sources, such as network devices, servers, and applications.
SIEM services help organizations to detect and respond to security incidents in real-time, and to comply with regulatory requirements. SIEM systems collect and analyze log data, network traffic, and other security-related data to identify potential security threats.
5. Compliance and Risk Management
Compliance and risk management is a type of cybersecurity service that involves helping organizations to comply with regulatory requirements and industry standards, such as HIPAA, PCI-DSS, and GDPR.
This service includes risk assessment, compliance consulting, and audit preparation. Compliance and risk management services help organizations to identify and mitigate security risks, and to ensure that their security controls are aligned with regulatory requirements.
6. Cloud Security
Cloud security is a type of cybersecurity service that involves protecting cloud-based infrastructure, applications, and data from cyber threats.
Cloud security services include cloud vulnerability assessment, cloud penetration testing, and cloud security monitoring. This type of service helps organizations secure their cloud-based assets and comply with cloud security standards, such as PCI-DSS and HIPAA.
7. Managed Security Services
Managed security services (MSS) is a type of cybersecurity service that involves outsourcing security operations to a third-party provider.
MSS providers offer a range of services, including security monitoring, incident response, and vulnerability management. MSS services help organizations to reduce security costs, improve security posture, and comply with regulatory requirements.
8. Security Consulting
Security consulting is a type of cybersecurity service that involves providing expert advice and guidance on security-related matters, such as security strategy, security architecture, and security policy development.
Security consultants help organizations to develop and implement effective security programs, and to address specific security challenges. Security consulting services include security assessments, security audits, and security awareness training.
9. Identity and Access Management (IAM)
Identity and Access Management (IAM) is a type of cybersecurity service that involves managing access to digital resources, such as networks, applications, and data. IAM services include identity management, access management, and authentication management.
This type of service helps organizations to ensure that only authorized users have access to sensitive resources and to comply with regulatory requirements, such as GDPR and HIPAA.
10. Cyber Security Awareness Training
Cyber Security awareness training is a type of cybersecurity service that involves educating users about cybersecurity best practices, such as phishing, password management, and safe browsing.
This type of service helps organizations to reduce the risk of security incidents caused by user error and to improve overall security posture. Cybersecurity awareness training services include online training modules, workshops, and phishing simulations.
How to Choose the Right Cybersecurity Service?
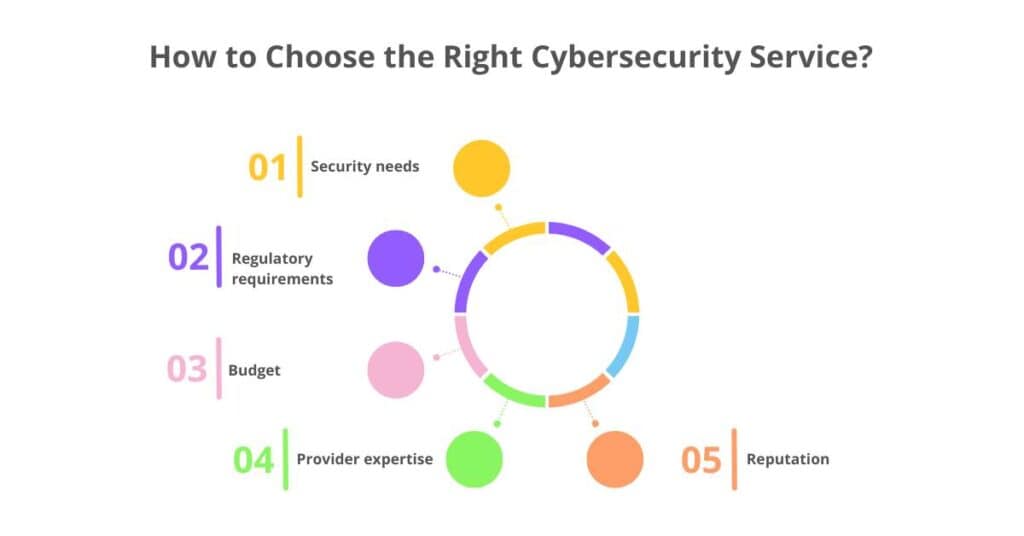
With so many different types of cybersecurity services available, it can be challenging to choose the right one for your organization. Here are some factors to consider when selecting a cybersecurity service:
1. Security needs
Identify your organization’s specific security needs, such as penetration testing, vulnerability assessment, or incident response.
2. Regulatory requirements
Consider the regulatory requirements that your organization must comply with, such as HIPAA, PCI-DSS, or GDPR.
3. Budget
Determine your budget for cybersecurity services and choose a service that fits within your budget.
4. Provider expertise
Choose a cybersecurity service provider with expertise in the specific area of cybersecurity that you need.
5. Reputation
Research the provider’s reputation and check for reviews and testimonials from previous clients.
Summary: Top 10 Different Types of Cyber Security Services
- Penetration Testing
- Incident Response
- Vulnerability Assessment
- Security Information and Event Management (SIEM)
- Compliance and Risk Management
- Cloud Security
- Managed Security Services
- Security Consulting
- Identity and Access Management (IAM)
- Cybersecurity Awareness Training
Conclusion:
In conclusion, there are various types of cybersecurity services available to help organizations protect their digital assets from cyber threats.
From penetration testing to cybersecurity awareness training, these services can help organizations identify and mitigate security risks, comply with regulatory requirements, and improve overall security posture.
By understanding the different types of cybersecurity services available, organizations can make informed decisions about their security needs and invest in the right services to protect their sensitive information.
FAQs: Top 10 Different Types of Cyber Security Services
1. What is the primary goal of cybersecurity services?
Ans: The primary goal of cybersecurity services is to protect an organization’s digital assets, such as sensitive data, systems, and networks, from cyber threats and attacks.
2. What types of organizations need cybersecurity services?
Ans: All types of organizations, including businesses, governments, and non-profit organizations, need cybersecurity services to protect their digital assets from cyber threats and attacks.
3. What is the difference between penetration testing and vulnerability assessment?
Ans: Penetration testing involves simulating a real-world attack on a computer system, network, or web application to test its defenses, while vulnerability assessment involves identifying and prioritizing vulnerabilities in an organization’s systems, networks, and applications.
4. How often should an organization conduct a cybersecurity risk assessment?
Ans: An organization should conduct a cybersecurity risk assessment at least once a year, or whenever there are significant changes to its systems, networks, or applications.
5. What is the role of incident response in cybersecurity services?
Ans: Incident response involves responding to and managing security incidents, such as data breaches, malware outbreaks, or denial-of-service (DoS) attacks, to minimize the damage and restore normal operations.
6. Can cybersecurity services be outsourced?
Ans: Yes, cybersecurity services can be outsourced to a third-party provider, such as a managed security services (MSS) provider, which can offer a range of services, including security monitoring, incident response, and vulnerability management.
7. is the importance of security awareness training in cybersecurity services?
Ans: Security awareness training is important in cybersecurity services because it helps to educate users about cybersecurity best practices, such as phishing, password management, and safe browsing, to reduce the risk of security incidents caused by user error.
8. How can an organization measure the effectiveness of its cybersecurity services?
Ans: An organization can measure the effectiveness of its cybersecurity services by tracking key performance indicators (KPIs), such as the number of security incidents, the response time to security incidents, and the overall security posture of the organization.
9. What is the role of cloud security in cybersecurity services?
Ans: Cloud security involves protecting cloud-based infrastructure, applications, and data from cyber threats and attacks, and is an important aspect of cybersecurity services for organizations that use cloud computing.
10. How can an organization choose the right cybersecurity service provider?
Ans: An organization can choose the right cybersecurity service provider by considering factors such as the provider’s expertise, reputation, and experience, as well as the services offered, the cost, and the level of support provided, to ensure that the provider can meet the organization’s specific cybersecurity needs.
