
Third-Party Risk Management: Strengthening Your Supply Chain with SOCs
In today’s interconnected world, businesses rely heavily on third-party vendors, partners, and suppliers to operate efficiently and scale their operations. While this collaboration boosts productivity, it also introduces a significant challenge: third-party risk. A single vulnerability in your supply chain can expose your business to cyber threats, compliance violations, and reputational damage.
This is where Security Operations Centers (SOCs) step in to safeguard not just your internal systems but also the extended network of third-party relationships. SOCs play a critical role in helping businesses mitigate risks, ensure compliance, and fortify their supply chains against emerging threats.
- Why Third-Party Risk Management Matters?
- The SOC’s Role in Third-Party Risk Management
- Real-Life Example: Third-Party Risk in Action
- Key Benefits of SOCs in Third-Party Risk Management
- How to Strengthen Your Third-Party Risk Management Strategy
- Explore More in Our SOC Series
- Conclusion: Securing Your Supply Chain with SOCs
Why Third-Party Risk Management Matters?

When you work with third-party vendors, you share sensitive information, grant access to critical systems, and depend on them to uphold security standards. But what happens if their security posture isn’t as robust as yours?
1. Supply Chain Attacks
Hackers often target vendors as a gateway to infiltrate larger organizations. The SolarWinds breach is a stark reminder of how damaging such attacks can be.
2. Data Breaches
A vendor’s weak security practices can lead to the exposure of sensitive data.
3. Compliance Violations
If your vendor fails to meet regulatory standards, your business could face fines, legal action, or reputational damage.
Managing third-party risks isn’t optional—it’s essential to protect your business and maintain trust with your stakeholders.
The SOC’s Role in Third-Party Risk Management

A SOC is your 24/7 cybersecurity guardian, monitoring threats and ensuring that your third-party relationships don’t become a liability. Here’s how SOCs strengthen third-party risk management:
1. Continuous Monitoring of Third-Party Networks
A SOC doesn’t just monitor your internal systems—it extends its vigilance to your vendors’ interactions with your network. This includes:
- Identifying unusual activity from third-party systems.
- Monitoring data exchanges between your business and vendors.
- Detecting and mitigating potential threats in real-time.
For example, if a vendor’s credentials are compromised and used to access your systems, the SOC will flag and respond to this activity before it escalates.
2. Vendor Risk Assessments
Before partnering with a vendor, it’s crucial to assess their security posture. SOCs assist by conducting:
- Vulnerability Assessments: Identifying weaknesses in a vendor’s systems.
- Compliance Checks: Ensuring the vendor meets industry standards like GDPR, HIPAA, or ISO 27001.
- Risk Scoring: Assigning a risk level to each vendor, helping you prioritize and address high-risk relationships.
3. Incident Response and Containment
When a third-party breach occurs, time is of the essence. SOCs are equipped with incident response playbooks that:
- Contain the breach to minimize damage.
- Notify relevant stakeholders, including regulators, when necessary.
- Provide actionable steps to remediate vulnerabilities and prevent future incidents.
4. Strengthening Supply Chain Security Posture
SOCs work proactively to ensure your supply chain is resilient against cyber threats by:
- Implementing strict access controls for vendors.
- Regularly auditing third-party activity within your network.
- Enforcing encryption standards for data shared with vendors.
5. Ensuring Compliance Across the Supply Chain
Many regulations, such as PCI DSS and GDPR, require businesses to ensure that their vendors comply with security standards. SOCs simplify this process by:
- Automating compliance checks and maintaining detailed records.
- Generating audit-ready reports to demonstrate compliance.
- Identifying non-compliant vendors and recommending corrective actions.
Real-Life Example: Third-Party Risk in Action
Imagine this scenario: Your marketing agency’s email platform is compromised, and the attacker uses it to send phishing emails to your customers. Without a SOC, you might only learn about the breach after significant damage has been done.
With a SOC, however, the unusual email activity would be flagged immediately. The SOC team would investigate, contain the threat, and guide both you and the vendor on remediation steps. By responding swiftly, the SOC minimizes damage, protects your customers, and safeguards your reputation.
Key Benefits of SOCs in Third-Party Risk Management
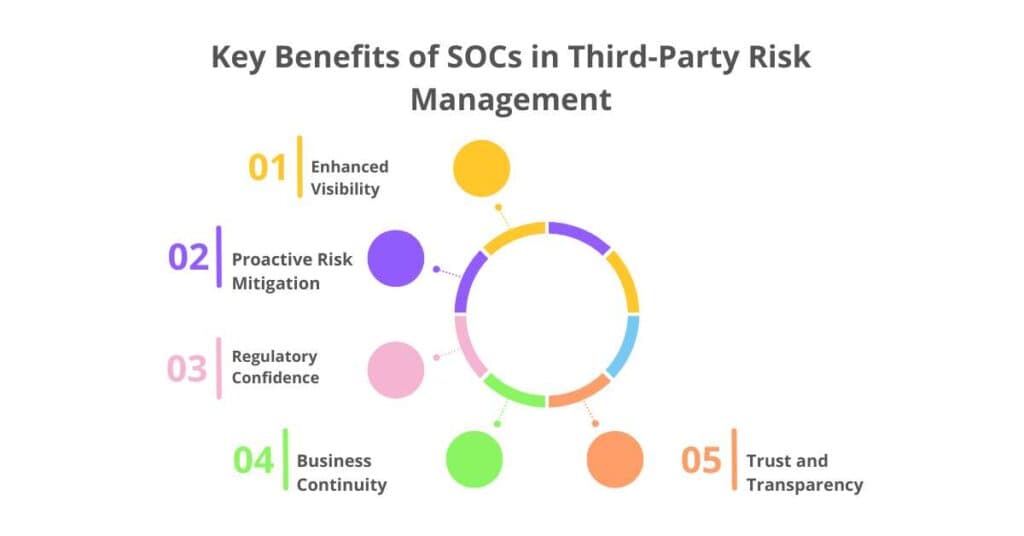
By integrating SOC services into your third-party risk management strategy, you gain:
1. Enhanced Visibility
A clear view of all vendor activity within your network.
2. Proactive Risk Mitigation
Early detection and response to third-party threats.
3. Regulatory Confidence
Assurance that your supply chain meets compliance requirements.
4. Business Continuity
Minimizing disruptions caused by third-party incidents.
5. Trust and Transparency
Building stronger relationships with vendors and customers alike.
How to Strengthen Your Third-Party Risk Management Strategy

To maximize the impact of SOC services, consider these best practices:
1. Conduct Regular Risk Assessments
Periodically evaluate the security posture of your vendors.
2. Limit Access
Grant vendors only the permissions they need to perform their tasks.
3. Establish Clear SLAs
Include cybersecurity requirements in your service-level agreements with vendors.
4. Invest in SOC Services
Partner with a SOC provider that understands your industry’s unique challenges and compliance needs.
Explore More in Our SOC Series
Strengthen your business’s cybersecurity with our SOC blog series, covering essential insights on Security Operations Centers (SOCs) and their role in protecting digital assets. Dive into expert guidance on SOC implementation, management, and the latest trends.
- Why Every Business Needs a SOC: Protecting Your Digital Assets
- Key Challenges in Cybersecurity for Enterprises and How SOCs Solve Them
- Customizing SOC Services for Enterprises: Aligning Security with Business Goals
- In-House vs. Managed SOC: Making the Right Choice for Your Business
- SOC-as-a-Service: Scalable Security for Growing Businesses
- How to Choose the Right SOC Partner for Your Business
- Measuring the ROI of SOCs: The Business Case for Cybersecurity
- Integrating SOC Services with Business Applications and Workflows: A Seamless Approach to Security
- Incident Response for Enterprises: SOC Playbooks in Action
- Ensuring Compliance with SOC Services Navigating Regulations Made Easy
- Third-Party Risk Management: Strengthening Your Supply Chain with SOCs
- Addressing Advanced Persistent Threats (APTs) with SOC Expertise
- The Role of Automation in SOC: Enhancing Detection and Response
- The Future of SOCs: Trends and Innovations for B2B Cybersecurity
Conclusion: Securing Your Supply Chain with SOCs
Third-party risks are a reality of doing business in today’s interconnected world. But with a robust SOC in your corner, you can confidently manage these risks, ensuring your supply chain remains secure and compliant.
A SOC doesn’t just protect your business—it protects the entire ecosystem you operate in, from vendors to customers. By extending its reach to third-party relationships, a SOC helps you build a resilient, secure, and trustworthy supply chain.
In a world where your reputation is only as strong as your weakest link, investing in SOC services is not just a smart decision—it’s a necessary one. So, take the first step today and strengthen your supply chain with the power of a SOC. Your business—and your customers—will thank you for it.
