Australian organizations in cyberspace now battle endlessly the cyber threats they experience. Phishing attacks, when cyber criminals try to obtain confidential and private information by impersonating organizations or famous entities, are one of the forms of threat that are most common.
Making sure that employees have enough knowledge to be able to identify and prevent such fraudulent schemes is of great importance.
Phishing simulation tools are an effective tool, they enable you to assess employees’ knowledge and skills as well as familiarize them with the risk of phishing and teach them how to defend against it.
In this blog, we have thoroughly researched and written a detailed guide on the Top 20 Best Phishing Simulation Tools that Every Australian Business Should Use.
Why Do Phishing Simulation Tools Matter?
Phishing emails are becoming increasingly sophisticated, often mimicking real companies and leveraging social engineering tactics to bypass suspicion. These emails can trick even the most vigilant employees. Here’s why simulation tools are essential
- Improved Employee Awareness: Simulations make employees textbook examples of phishing defence tactics enabling them to be quick in pausing when they encounter a suspicious email that is harmful.
- Reduced Risk of Data Breaches: The initiation of internal policies that educate employees to easily identify phishing fraud, decreases the odds of companies’ confidential data being stolen.
- Enhanced Security Culture: Organizing simulations of cybersecurity on a regular basis is a good way to build a culture where the employees are more vigilant with regard to online safety.
- Compliance with Regulations: There are several businesses in Australia whose data security policy has had employees trained on phishing awareness.
List of Top 20 Best Phishing Simulation Tools that Every Australian Business Should Use

1. PhishCare by CyberSapiens: Best Phishing Simulation Tools
Cyber Sapiens offers phishing simulation services through their phishing tool called “PHISH CARE”. Here you can also run a free Simulation. This tool offers a comprehensive phishing test designed to improve awareness of phishing scams across organizations.
CyberSapiens provides various phishing scenarios, easy reporting, and tailored templates for different industry sectors
Best Benefits of “PhishCare” Tool
- End to End Tracking capability
- Spear phishing
- Fully customized templates
- Follow up Training
- In-Depth Reporting
- Security Checkpoint
Best Features of “PhishCare” Tool
- Customized Templates
- Awareness Module
- Assessment Test
- Comprehensive Tracking
- Graphical dashboard Access
- Campaign Report
- Custom domain integration
CyberSapiens highlighted that 47% of cyber security attacks such as social engineering, spear-phishing, and ransomware attacks are financially motivated, and it’s crucial to test employees and make them proactive in identifying and reporting phishing attacks
For organizations interested in enhancing their phishing awareness and defence, CyberSapiens provides a service that not only tests employees’ susceptibility to phishing but also educates them on how to recognize and avoid falling victim to such scams.
This proactive approach is essential in today’s environment where cyber attacks are prevalent and increasingly sophisticated

2. KnowBe4
Being a globally recognised leader, KnowBe4 offers the company’s customers an efficient platform for simulated phishing with a huge repertoire of customizable templates that the clients can personalize to suit their situations. They give vocational work training by including games and rich report-generation features to monitor employee progress.
3. Cofense PhishMe
Besides, it is this cloud-based platform that is used for phishing simulations that are automated and their campaigns are aimed at employees in different roles and departments. PhishMe is in its possession various alerting mechanisms that empower the organization to respond to and act on suspicious emails.
4. Mimecast
This email security remedy applies phishing simulation functionalities using filtering and anti-malware tools amongst others. Mimecast is due to be on the list of email security software for companies that insist on having all-in-one solutions with features for simulation training.
5. Honeypot
This open-source platform economizes on the technical and privileged information validation forced by phishing attacks by providing entrepreneurs with a cost-effective option for phishing simulations. But Honeypot needs to be installed and configured by experts thus not available to companies that do not have IT security personnel.
6. Sim Phish
It is a user-friendly platform at which some templates of phishing minimum alone and gives employees live instructions that are accessed by simulation.
7. Proofpoint
Using more extensive than traditional phishing simulation customized training paired with personalized learning, a leading enterprise security technology provider, Proofpoint, enables its users.
8. SpamTitan Phishing Simulator
This tool proves to be a cost-efficient mechanism to do some initial phishing simulations that connect to SpamTitan’s email security platform to further the anti-phishing campaign.
9. IT Governance Phishing Simulator
In this leaderboard UK company, there are spamming samples you can use to make your campaign more useful to customers and specialists.
10. Cloud Phish
Cloud Phish refers to a cloud-based phishing simulation tool that lets businesses set up as well as measure subjected to phishing rates.
11. Gophish
Gophish is an open-source phishing simulation tool that can assist businesses by allowing them to develop phishing simulations that appear real and enable them to track the click-through rates of their employees.

12. PhishTank
PhishTank is a social media platform in which users create a database of phishing emails to raise awareness and train each other to identify phishing attacks.
13. OpenPhish
OpenPhish is an open-source tool that enables businesses to build believable phishing simulators and monitor employee interaction with emails.
14. Netsparker Web Application Security Scanner
The web security scanner Netsparker Web Application is a detecting pluckers who may be involved in phishing websites.
15. DeceptionPoint
DeceptionPoint is an internet deception technology company used for the detection and identification of phishing attacks.
16. F-Secure Radar
F-Secure Radar is the fitness of a cloud-based endpoint which includes protection against phishing.
17. Cisco AMP for Endpoints
Alongside these components, Cisco AMP for Endpoints is an endpoint protection platform that additionally provides a phishing protection feature.
18. CrowdStrike Falcon Endpoint Protection
CrowdStrike Falcon Endpoint Protection is a single-agent platform that uses slips of identity to confirm user credentials during login and to secure emails.
19. Phished
Phished is a user-friendly phishing simulation tool that allows businesses to create realistic phishing simulations and track employee click-through rates.
20. McAfee Endpoint Security
McAfee Endpoint Security is an integrated endpoint protection platform with email phishing features.
Choosing the Right Phishing Simulation Tool
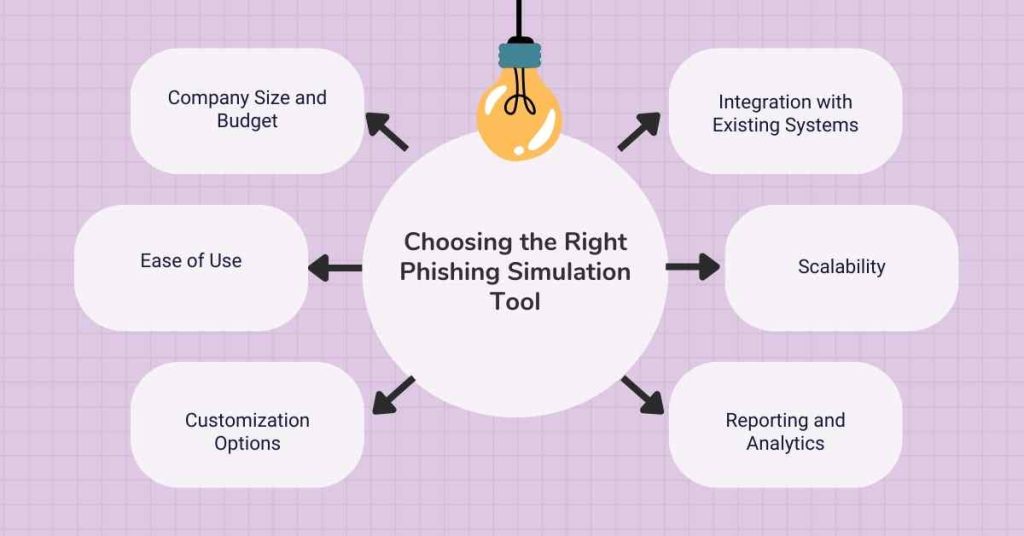
With so many options available, selecting the ideal phishing simulation tool requires careful consideration of your company’s specific needs. Here are some key factors to evaluate:
1. Company Size and Budget
Pricing models are quite diverse from those offering free-of-charge applications and those others being monthly subscriptions for specific users. Ponder over the amount of money you can easily allocate for training, and the number of employees you would want trained.
2. Ease of Use
Search for software that has easy-to-use functioning and is navigable by even the least tech-inclined individuals. With such features of the computer, ongoing campaign creation and reporting are as simple.
3. Customization Options
Personalization of phishing templates that reflect real-world circumstances in your industry, area or downright financial interests is a must-have.
4. Reporting and Analytics
Comprehensive review mechanisms focus on raising the tokens of employees’ opinions about security issues and discovering things that need more training and attention.
5. Scalability
As the business expands and grows, make sure the system can easily be scaled up at any time to fit more employees and training requirements.
6. Integration with Existing Systems
Set if the tool functions jointly with your present security with the likes of email safeguards or learning management systems or not.
Summary: Top 20 Best Phishing Simulation Tools that Every Australian Business Should Use
- PhishCare by CyberSapiens
- KnowBe4
- Cofense PhishMe
- Mimecast
- Honeypot
- Sim Phish
- Proofpoint
- SpamTitan Phishing Simulator
- IT Governance Phishing Simulator
- Cloud Phish
- Gophish
- PhishTank
- OpenPhish
- Netsparker Web Application Security Scanner
- DeceptionPoint
- F-Secure Radar
- Cisco AMP for Endpoints
- CrowdStrike Falcon Endpoint Protection
- Phished
- McAfee Endpoint Security
Conclusion
Finding and exploiting the gap in human knowledge can be done very easily through phishing simulations. However, the business can prevent being exploited by these cybercrime activities by using phishing tools.
Through the identification of appropriate tools and by conducting a systematic approach, businesses will be able to handle this threat more successfully.
Recall the fact that alert and sharp workers are the most powerful weapon against potential cybercrimes which is impossible to stop with any other security system.
FAQs
1. Are phishing simulation tools legal in Australia?
Ans: Absolutely Phishing simulation tools are a legitimate and encouraged practice for Australian businesses to raise security awareness and comply with data protection regulations.
2. How often should I run phishing simulations?
Ans: Regularity is key. Aim for monthly or quarterly simulations to keep employees vigilant and on their toes.
3. What happens if an employee clicks on a simulated phishing link?
Ans: The outcome depends on the chosen tool. Typically, they’ll be redirected to a landing page explaining it was a simulated attack and providing educational resources on phishing identification.
4. Do phishing simulation tools integrate with other security software?
Ans: Yes, many tools offer integration with existing email security platforms and learning management systems, streamlining your security posture.
5. What are the benefits of using an Australian-based phishing simulation tool?
Ans: Some Australian tools offer pre-built templates tailored to local threats and industry scenarios, making them more relevant to your employees.
6. Can I use a free phishing simulation tool?
Ans: Several vendors offer freemium plans with limited features. However, for comprehensive functionality and employee training, paid plans are often recommended.
7. How can I measure the effectiveness of my phishing simulation campaigns?
Ans: Most tools provide detailed reports on employee click rates, response times, and overall awareness levels.
8. What’s the difference between phishing simulations and security awareness training?
Ans: Simulations provide a hands-on experience, while training offers broader knowledge on various cyber threats. Both are crucial for a layered defence strategy.
9. Is it okay to trick employees with phishing simulations?
Ans: The goal is to educate, not humiliate. Simulations should be realistic but not stressful, with clear post-attempt explanations and opportunities for learning.
10. How can I get buy-in from leadership for implementing phishing simulations?
Ans: Highlight the financial cost of potential data breaches and the importance of a proactive cybersecurity culture for employee and customer protection.